Russian Military Intelligence Leverages Older Routers to Mass Harvest Microsoft Office Authentication Tokens
Hackers unequivocally linked to Russia’s military intelligence units have been exploiting known vulnerabilities in outdated Internet routers to conduct a widespread campaign, quietly siphoning authentication tokens from Microsoft Office users across more than 18,000 networks. This sophisticated yet remarkably low-tech spying operation, brought to light by security experts, allowed state-backed Russian hackers to gain access without deploying any traditional malicious software or code on victim devices, highlighting a persistent and evolving threat to global cybersecurity.
The Attack Unveiled: Modus Operandi and Token Theft
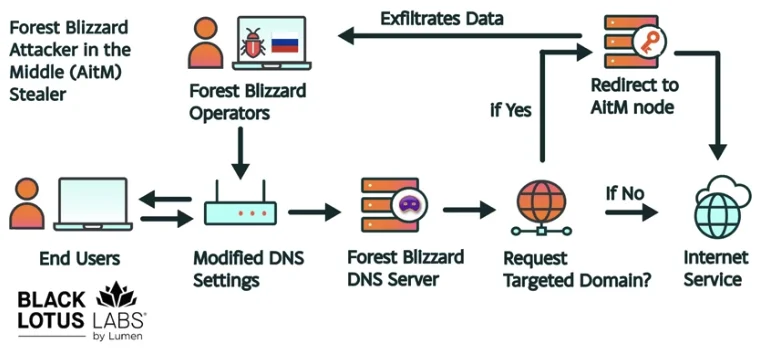
The core of this espionage campaign revolves around a technique known as DNS hijacking, coupled with adversary-in-the-middle (AiTM) attacks. As detailed by security researchers at Black Lotus Labs, a division of Internet backbone provider Lumen, the threat actor, identified as "Forest Blizzard" (also known as APT28 or Fancy Bear), targeted small office/home office (SOHO) routers, primarily older Mikrotik and TP-Link devices. These routers, often unsupported, end-of-life, or significantly behind on security updates, presented a fertile ground for exploitation.
Instead of planting malware, the GRU-affiliated hackers leveraged known flaws in these vulnerable devices to alter their Domain Name System (DNS) settings. DNS, often referred to as the internet’s phonebook, translates human-readable website names (like "google.com") into machine-readable IP addresses. By redirecting DNS queries to their own controlled servers, the attackers could then covertly steer users to malicious websites or proxies designed to intercept sensitive information.
Crucially, this allowed Forest Blizzard to propagate their malicious DNS settings to all users connected to the compromised local network. From that point forward, any OAuth authentication tokens transmitted by those users could be intercepted. OAuth tokens are digital keys issued after a user successfully logs in, allowing applications to access specific resources on their behalf without requiring re-entry of credentials. Because these tokens are typically generated after a user has completed the login process, including multi-factor authentication (MFA), the attackers could bypass the need to phish credentials or one-time codes. This direct acquisition of valid authentication tokens granted the hackers unhindered access to victim accounts, effectively bypassing layers of modern security designed to protect against credential theft.
Ryan English, a Security Engineer at Black Lotus Labs, underscored the cunning simplicity of the approach: "Everyone is looking for some sophisticated malware to drop something on your mobile devices or something. These guys didn’t use malware. They did this in an old-school, graybeard way that isn’t really sexy but it gets the job done." This sentiment highlights a critical lesson in cybersecurity: sometimes the most effective attacks exploit fundamental infrastructure weaknesses rather than zero-day software vulnerabilities.
Microsoft corroborated these findings in a blog post, referring to the Forest Blizzard activity as using DNS hijacking "to support post-compromise adversary-in-the-middle (AiTM) attacks on Transport Layer Security (TLS) connections against Microsoft Outlook on the web domains." While targeting SOHO devices is not a novel tactic, Microsoft noted that this represents the first instance they have observed Forest Blizzard utilizing "DNS hijacking at scale to support AiTM of TLS connections after exploiting edge devices." This signifies a strategic evolution in the group’s operational methodology, moving from more targeted, malware-centric attacks to broad-spectrum infrastructure compromise.
Forest Blizzard: A Persistent and Adaptable Threat
The threat actor "Forest Blizzard" is not a new entrant to the geopolitical cyber landscape. It is widely attributed to the military intelligence units within Russia’s General Staff Main Intelligence Directorate (GRU) and is also known by other prominent names such as APT28 and Fancy Bear. This group has a long and notorious history of state-sponsored cyber espionage and disruptive operations targeting governments, political organizations, and critical infrastructure worldwide.
Perhaps their most infamous operation was the compromise of the Hillary Clinton campaign, the Democratic National Committee (DNC), and the Democratic Congressional Campaign Committee (DCCC) in 2016. This campaign, which involved spear-phishing attacks and subsequent leaking of stolen emails, was a significant attempt to interfere with the U.S. presidential election and has since become a benchmark for state-sponsored election interference. The group’s activities consistently align with Russia’s strategic interests, including intelligence gathering, influence operations, and disruption.
Their operational sophistication is matched by their adaptability. As this latest campaign demonstrates, Forest Blizzard is adept at shifting tactics in response to detection and public disclosure. This agility allows them to maintain persistence and effectiveness even when their methods are exposed.
Scale and Scope of the Operation
The scale of this recent operation is substantial. According to Black Lotus Labs, at the peak of its activity in December 2025, Forest Blizzard’s surveillance dragnet ensnared more than 18,000 Internet routers. This vast network of compromised devices served as the launchpad for their token harvesting campaign.
Microsoft’s internal analysis identified over 200 organizations and 5,000 consumer devices that were directly caught up in this stealthy spying network. The primary targets, as highlighted by Lumen’s report, were government agencies, including ministries of foreign affairs, law enforcement entities, and third-party email providers. This targeting profile underscores the strategic intelligence objectives of the GRU, aiming to gather sensitive information from critical governmental and diplomatic channels. The inclusion of third-party email providers further emphasizes the potential for supply chain attacks, where compromising a service provider grants access to multiple downstream clients.
The impact extends beyond the immediate victims. The ability to harvest authentication tokens from thousands of users on thousands of networks creates a significant intelligence advantage, allowing the GRU to maintain long-term access to compromised accounts, monitor communications, and exfiltrate data without triggering conventional malware detection mechanisms.
The Vulnerability: SOHO Routers and Legacy Devices
The exploitation of SOHO routers, particularly older and unsupported models, highlights a pervasive and often overlooked vulnerability in the global internet infrastructure. These devices, designed for small businesses and home users, are frequently deployed and then forgotten, rarely receiving the necessary security updates or proper configuration.
The lifecycle of consumer-grade networking equipment is a significant factor. Many users replace their computers and phones regularly but keep routers for years, even after manufacturers cease providing security patches. This creates a vast attack surface of devices with known, unpatched vulnerabilities that can be easily exploited by determined adversaries. The relatively low cost and widespread deployment of these devices also make them attractive targets for mass exploitation. Attackers can achieve broad impact by compromising a large number of these less-secure "edge" devices, which then serve as entry points into more secure internal networks.

The U.K.’s National Cyber Security Centre (NCSC) issued its own advisory detailing how Russian cyber actors have been compromising routers, reinforcing the gravity of the situation. The NCSC explained that DNS hijacking attacks interfere with the fundamental process of how users access websites, covertly redirecting them to malicious sites or proxy servers designed to steal login details or other sensitive information. This foundational attack vector underscores the importance of securing network infrastructure at its most basic level.
Expert Insights and Official Confirmations
The coordinated disclosure by Microsoft, Lumen’s Black Lotus Labs, and the NCSC provides a comprehensive view of the threat. Microsoft’s blog post, released on April 7, 2026, served as a crucial official confirmation of the campaign, offering detailed technical analysis and mitigation guidance. The company’s identification of "Forest Blizzard" as the perpetrator, along with their specific observations of the AiTM techniques, adds significant weight to the findings.
Lumen’s Black Lotus Labs report, published concurrently, provided the initial detailed technical breakdown of the operation, including the scale of compromised routers and the specific types of devices targeted. Their researchers, Ryan English and Danny Adamitis, offered valuable insights into the "old-school" nature of the attack and the threat actor’s demonstrated adaptability.
The NCSC’s advisory complemented these reports by providing a broader context of Russian state-sponsored cyber activity targeting routers, emphasizing the critical role of DNS in these attacks and offering practical advice for protection. The synergy between these organizations in publicly disclosing the threat aims to raise awareness and prompt defensive actions across affected sectors.
Chronology of Discovery and Response
The timeline of this campaign reveals a reactive and adaptable adversary. While the peak activity of Forest Blizzard’s surveillance dragnet was observed in December 2025, the group’s tactical evolution can be traced back earlier.
In August 2025, the NCSC released a separate report (PDF) detailing previous Forest Blizzard activities, which at the time involved using malware to control a far more targeted and smaller group of compromised routers. According to Danny Adamitis of Black Lotus Labs, Forest Blizzard immediately switched up its tactics in response to this NCSC report. "Before the last NCSC report came out they used this capability in very limited instances," Adamitis told KrebsOnSecurity. "After the report was released they implemented the capability in a more systemic fashion and used it to target everything that was vulnerable." This pivot from malware-centric, targeted attacks to a broad, infrastructure-level DNS hijacking campaign underscores their ability to learn, adapt, and scale their operations quickly in the face of public disclosure.
The current wave of disclosures on April 7, 2026, by Microsoft, Lumen, and the NCSC, serves as a fresh warning, forcing Forest Blizzard to potentially reconsider their current methods once again. The constant cat-and-mouse game between threat actors and cybersecurity researchers is a defining characteristic of modern cyber warfare.
Adding another layer to the discussion around router security, on March 23, 2026, the U.S. Federal Communications Commission (FCC) announced a significant policy shift. Moving beyond a proposed ban on specific manufacturers like TP-Link, the FCC declared it would no longer certify consumer-grade Internet routers produced outside of the United States. The commission justified this drastic measure by citing foreign-made routers as an "untenable national security threat," arguing that poorly-secured devices could "immediately and severely disrupt U.S. critical infrastructure and directly harm U.S. persons." This broader approach aims to address the systemic vulnerabilities highlighted by incidents like the Forest Blizzard campaign, though it has sparked debate regarding its practical implications for the availability and cost of consumer networking equipment.
Broader Implications: Geopolitics and Cybersecurity
This incident highlights several critical implications for national security and global cybersecurity. Firstly, it reaffirms the persistent and sophisticated nature of state-sponsored cyber espionage, particularly from nations like Russia. The GRU’s willingness to invest in and adapt complex cyber operations underscores the strategic value they place on intelligence gathering through digital means.
Secondly, the reliance on known vulnerabilities in legacy SOHO devices exposes a significant weakness in the collective digital defense. While enterprises often invest heavily in advanced security solutions, the "edges" of the network, particularly home and small office environments, remain soft targets. These devices are often the weakest link, providing an indirect pathway into more secure corporate networks as employees work remotely or use personal devices for work-related tasks.
Thirdly, the FCC’s recent policy regarding foreign-made routers, while not directly addressing the current compromised devices (as it only applies to future certifications), is a governmental response to the broader concern of supply chain security in networking hardware. Experts have raised questions about the policy’s feasibility, noting that few new consumer-grade routers would be available under this strict mandate, aside from niche products like Starlink routers manufactured in the U.S. The policy allows for "conditional approval" from the Department of War or Department of Homeland Security, suggesting a complex new regulatory landscape for router manufacturers. This debate underscores the tension between national security imperatives and the realities of a globalized electronics manufacturing industry.
Finally, the incident serves as a stark reminder that even "old-school" hacking techniques can be devastatingly effective. The emphasis on sophisticated malware often overshadows the impact of fundamental network layer attacks. This campaign proves that a deep understanding of network protocols and an opportunistic approach to exploiting widely known, unpatched vulnerabilities can yield significant intelligence gains.
Mitigation and Recommendations
Given the nature of this attack, several mitigation strategies are crucial for individuals and organizations:
- Update Router Firmware: Regularly check for and install the latest firmware updates from router manufacturers. Many SOHO routers have automatic update features that should be enabled. For end-of-life devices, consider replacing them.
- Replace End-of-Life Routers: If a router is no longer receiving security updates, it is a significant risk and should be replaced with a modern, actively supported model.
- Strong Passwords and Unique Credentials: Ensure routers are secured with strong, unique administrator passwords, not default credentials.
- Review DNS Settings: Periodically check router DNS settings to ensure they point to legitimate, trusted DNS servers (e.g., those provided by your ISP or public DNS services like Cloudflare 1.1.1.1 or Google 8.8.8.8). Any unexpected or unknown DNS server addresses should be investigated immediately.
- Enable Multi-Factor Authentication (MFA): While this attack bypassed MFA during token use, robust MFA still protects against direct credential theft and is a fundamental security best practice for all online accounts, especially for Microsoft Office 365.
- Network Segmentation: For businesses, segmenting networks can limit the lateral movement of attackers even if an edge device is compromised.
- Employee Education: Train employees on the risks of using insecure home networks for work-related activities and the importance of secure device management.
- Monitor for Suspicious Activity: Organizations should monitor network traffic for unusual DNS queries or connections to unfamiliar IP addresses.
The Evolving Cyber Landscape
The Forest Blizzard campaign serves as a powerful testament to the ever-evolving nature of cyber warfare. It demonstrates that state-sponsored actors are not solely reliant on cutting-edge zero-day exploits but can achieve widespread impact by exploiting fundamental weaknesses in widely deployed, often neglected, infrastructure. As governments grapple with the implications for national security and critical infrastructure, the responsibility also falls on individuals and organizations to adopt proactive security measures. The battle for digital sovereignty will continue to be fought not just in the realm of advanced malware, but also in the less glamorous, yet critically important, domain of router security and network hygiene.