Cybersecurity
-
Global Law Enforcement Dismantles Aisuru, Kimwolf, JackSkid, and Mossad Botnets, Halting Record-Breaking IoT DDoS Attacks
A monumental international collaboration between the U.S. Justice Department, Canadian, and German authorities has successfully dismantled the intricate online infrastructure…
Read More » -

Defense in Depth, Medieval Style: Unpacking the Engineering Marvel of Constantinople’s Theodosian Walls
The Theodosian Walls of Constantinople stand as one of history’s most extraordinary feats of military engineering, a testament to strategic…
Read More » -

Lockbit Dominates Ransomware Landscape as Conti Offshoots Drive Significant Resurgence in Cyberattacks
A notable resurgence in ransomware attacks has been observed this summer, with Lockbit firmly establishing itself as the most prolific…
Read More » -

Payouts King Ransomware Leverages QEMU Virtual Machines for Covert Operations and Advanced Evasion
The Payouts King ransomware operation has escalated the sophistication of its attacks by deploying the QEMU emulator as a reverse…
Read More » -

Microsoft Defender Under Siege: Threat Actors Exploit Multiple Zero-Day Vulnerabilities for Privilege Escalation and Service Disruption
A critical warning has been issued by cybersecurity firm Huntress, indicating that sophisticated threat actors are actively exploiting a trio…
Read More » -
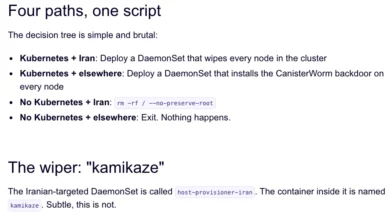
Financially Motivated Cybercrime Group TeamPCP Unleashes Data-Wiping Worm Targeting Iranian Systems Amidst Escalating Global Cyber Conflict
A sophisticated and financially driven data theft and extortion collective, known as TeamPCP, has intensified its operations by deploying a…
Read More » -

Human Trust of AI Agents
The research, titled "Humans expect rationality and cooperation from LLM opponents in strategic games," presents the findings of the first…
Read More » -

Massive Phishing Campaign Exploits Multi-Factor Authentication, Compromising Over 130 Organizations and Nearly 10,000 Accounts
A sprawling and highly effective phishing campaign, dubbed "0ktapus" by cybersecurity researchers, has ensnared more than 130 companies and compromised…
Read More » -

NAKIVO v11.2: Ransomware Defense, Faster Replication, vSphere 9, and Proxmox VE 9.0 Support
Sparks, Nevada – April 3rd, 2026 – NAKIVO Inc., a global leader in data protection trusted by over 16,000 organizations…
Read More » -

Threat Actors Unleash Mirai Variants via Vulnerabilities in TBK DVRs and End-of-Life TP-Link Routers
Cybersecurity researchers have issued urgent warnings regarding active exploitation campaigns leveraging critical security flaws in TBK Digital Video Recorders (DVRs)…
Read More »