The Unforeseen Triumph: Apple’s MacBook Neo Outshines the iPhone 17e in Entry-Level Value
Apple’s financial engine continues to be powered by the iPhone, with the iconic smartphone consistently accounting for approximately half of the company’s substantial revenue. This deep reliance on its mobile flagship makes it all the more striking that the technology giant has seemingly managed to craft a superior entry-level laptop experience with the new MacBook Neo, surpassing the value proposition offered by its latest budget iPhone, the iPhone 17e.
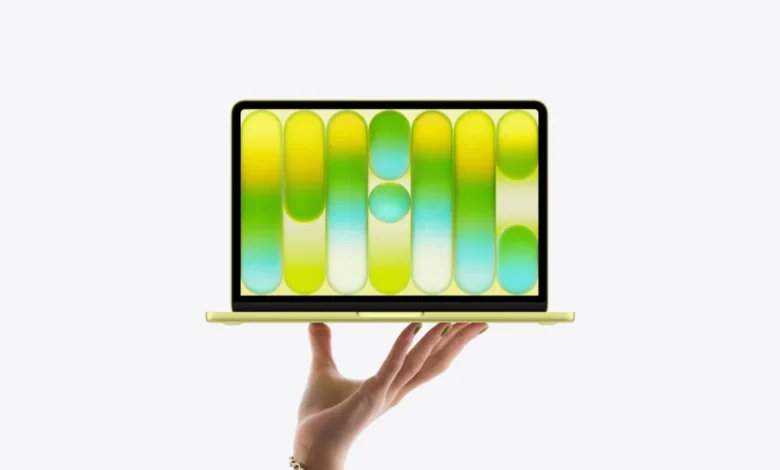
Launched at a competitive $599 in the United States, the MacBook Neo presents a compelling package that belies its accessible price point. Buyers are greeted with a robust, all-aluminum chassis, a vibrant 13-inch Liquid Retina display boasting impressive resolution, and the efficiency of Apple Silicon. Crucially, it delivers all-day battery life, a hallmark of Apple’s portable computing devices. Apple has been transparent about the Neo’s positioning; it is explicitly not a "Pro" machine designed for demanding workflows, eschewing the most powerful M-series processors. Nevertheless, despite these strategic hardware concessions, the MacBook Neo emerges as a remarkably complete and thoughtfully designed product, fostering a sense of genuine value for consumers.
In stark contrast, the iPhone 17e, also priced at $599, operates under the familiar philosophy of an entry-level iPhone. However, it struggles to evoke the same level of consumer satisfaction or perceived value. While it does incorporate an upgraded A19 chip for enhanced performance, introduces MagSafe compatibility, and doubles the base storage to a more practical 256GB, these improvements, though welcome, feel incremental rather than transformative. While earlier reports indicated that Apple had begun to address the perennial shortcomings of its budget iPhone offerings, the MacBook Neo’s arrival has illuminated a significant disparity in Apple’s approach to its most affordable product categories. The Neo achieves a sense of generosity, while the iPhone 17e, by comparison, still feels like a meticulously calculated exercise in compromise.
The Generous Mac Versus the Constrained iPhone
This disparity forms the crux of a burgeoning discussion within the tech community and among consumers. The MacBook Neo, despite its inherent limitations as an entry-level device, possesses an undeniable authenticity that aligns it with the broader Mac family. It doesn’t feel like a product merely designed to ensnare users into the Apple ecosystem; rather, it appears to have been engineered with the explicit goal of excelling within its market segment. Apple has endowed it with premium materials like the aluminum unibody, a high-quality display, a silent and efficient fanless design, and clear targeting towards students, families, and first-time Mac purchasers.
The market’s reception has been overwhelmingly positive, with initial demand reportedly exceeding Apple’s forecasts. Industry sources suggest that Apple has been compelled to accelerate production orders for the MacBook Neo, a testament to its unexpected popularity. This surge in demand underscores a consumer desire for accessible yet capable computing solutions that the Neo appears to fulfill.
Conversely, the iPhone 17e, while not a fundamentally flawed device, embodies Apple’s "just enough" philosophy to a degree that leaves many wanting more. The inclusion of the A19 chip, the long-awaited MagSafe support, and increased storage are indeed positive steps. However, the device retains the characteristic "e" designation, signaling its budget-oriented nature. It features a single rear camera, a conventional notch in lieu of the more advanced Dynamic Island found on higher-tier models, and conveys a message of limited access to the full iPhone experience.
When juxtaposed with the standard iPhone 17, the absence of ProMotion technology on the iPhone 17e becomes particularly apparent, making it feel like an "old-generation" smartphone at its price point. The solitary rear camera further exacerbates this perception. Competitors like Google’s Pixel 10a, for instance, offer a far more compelling value proposition in their respective entry-level tiers, providing smoother display technology and more versatile camera systems, even with smaller sensors. The iPhone 17e, in this context, forces users to make compromises in both display fluidity and photographic capability.

The MacBook Neo’s Unexpected Ascent in the Laptop Arena
The current economic climate, particularly the escalating costs associated with AI development and component sourcing, has exerted upward pressure on laptop prices across the industry. This has led to Arm-based laptops, initially envisioned as cost-effective alternatives to traditional x86 machines, increasingly encroaching upon the price territories traditionally occupied by more premium devices like the MacBook Air and MacBook Pro. This trend, combined with the lingering effects of global supply chain disruptions, has made the Windows ecosystem appear less attractive in terms of overall value for many consumers.
These inflationary pressures have also permeated the smartphone market, with numerous Android manufacturers adopting pricing strategies that mirror or even exceed those of Apple’s iPhones. It is within this challenging economic landscape that the MacBook Neo has managed to carve out a distinct and successful niche, while the iPhone 17e appears to be struggling to maintain relevance.
The core argument presented is that the MacBook Neo actively reshapes the conversation around affordable technology, offering a genuinely compelling proposition. The iPhone 17e, in contrast, seems content to merely survive within its established market segment.
The contrast in Apple’s product strategy becomes even more pronounced when one recalls the playful and distinctive approach the company once took with its entry-level iPhones. The resurgence of interest in the iPhone 5c, for example, is often attributed to its vibrant color options and a design that eschewed the seriousness and sterility often associated with premium electronics. It offered a sense of personality and fun, elements that are conspicuously absent from the iPhone 17e. The MacBook Neo, in a surprising turn of events, seems to have recaptured some of that lost design spirit, while the iPhone 17e continues to project an image of caution, as if Apple is hesitant to allow its most affordable smartphone to possess a distinct identity.
Apple’s Unintended Revelation: Where Further Development is Needed
The iPhone 17e is by no means a commercial failure or a poorly conceived product. It represents a tangible improvement over its predecessor and will undoubtedly find favor with a segment of consumers prioritizing brand loyalty and core iPhone functionality. However, the MacBook Neo stands as a more ambitious and successful endeavor in the entry-level market. Apple has infused it with an element of excitement, thoughtful design, and a disruptive quality that challenges conventional expectations for budget devices. This accomplishment, ironically, has been achieved with a laptop, a product category that is not the company’s primary revenue driver, rather than with its flagship mobile device.
In a significant development, Apple’s most affordable computer has emerged as one of the most compelling value propositions within its entire product lineup. Conversely, its most affordable new iPhone continues to feel like a purchase driven by brand allegiance rather than a genuine belief in exceptional value. For a company whose identity is so intrinsically linked to the iPhone, this misstep in its entry-level smartphone strategy is a particularly noteworthy observation.
A Shifting Market Landscape and Consumer Expectations
The evolution of the technology market over the past decade has seen a democratization of features previously reserved for premium devices. However, this trend has not been uniform across all product categories or price points. The advent of powerful mobile chipsets, advancements in display technology, and the increasing integration of AI capabilities have driven innovation but also contributed to rising production costs.
For instance, the integration of AI into various computing tasks, from image processing to natural language understanding, has placed a premium on memory and processing power. This "AI memory crunch," as it has been described, has directly impacted the cost of components, forcing manufacturers to pass these increases onto consumers. This is particularly evident in the laptop market, where even devices marketed as budget-friendly are now approaching price points that were once considered mid-range.

The timeline of these market shifts can be traced back several years. Initially, companies like Qualcomm and MediaTek made significant strides in developing powerful mobile processors that found their way into a wide array of Android smartphones, offering performance that rivaled or even surpassed earlier flagship iPhones at a fraction of the cost. This created a competitive pressure that Apple initially met by segmenting its iPhone lineup, introducing the "SE" and later the "e" models to cater to a more price-sensitive demographic.
However, the strategy of offering a stripped-down iPhone experience at a lower price point has become increasingly difficult to sustain as the technological gap between high-end and low-end models widens. The iPhone 17e, for example, faces criticism for retaining features like a single rear camera and a standard notch, while the Pro models boast advanced camera arrays and the Dynamic Island. This creates a perception of technological stagnation in the entry-level segment.
Strategic Positioning and Consumer Perception
Apple’s strategic decision-making in product development is often lauded for its precision. However, the MacBook Neo’s success highlights a potential disconnect in its approach to the entry-level smartphone market. The Neo appears to have benefited from a clear vision: to deliver a premium build and user experience at an accessible price, targeting a specific user base without significant compromises on core usability. This has resonated strongly with consumers, leading to unexpected demand and reportedly prompting Apple to increase production.
The implications of this are significant. It suggests that consumers are actively seeking value, and when a company like Apple, known for its premium pricing, delivers on that front, the response can be overwhelmingly positive. This could potentially influence Apple’s future product development strategies, encouraging them to re-evaluate their approach to the entry-level iPhone.
Conversely, the iPhone 17e’s struggle to capture the same level of enthusiasm can be attributed to its perceived lack of differentiation and its reliance on older design cues. While the inclusion of MagSafe and increased storage are practical upgrades, they do not fundamentally alter the user experience in a way that justifies the $599 price tag for many consumers, especially when compared to the tangible quality and completeness offered by the MacBook Neo.
Industry analysts have noted that the success of the MacBook Neo could put pressure on Apple to reconsider its strategy for the iPhone 17e and future budget iPhones. "Apple has demonstrated with the MacBook Neo that it can deliver a genuinely desirable product at a compelling price point," stated Sarah Chen, a senior analyst at Tech Insights. "The contrast with the iPhone 17e is stark. Consumers are increasingly savvy about value, and Apple’s historically strong brand loyalty might not be enough to overcome a perceived lack of innovation or a feeling of being short-changed, especially when competitive Android devices are offering more for similar money."
The broader impact of this situation extends beyond Apple’s immediate sales figures. It signals a potential shift in consumer expectations, particularly for entry-level devices. If Apple can deliver exceptional value in its laptop segment, consumers will naturally expect a similar level of consideration for its smartphones. The company’s historical success has been built on creating aspirational products, and while the iPhone remains a dominant force, the MacBook Neo’s triumph suggests that aspiration can also be achieved through thoughtful, value-driven design, even at the lower end of the market. This might compel Apple to imbue its future entry-level iPhones with more personality and a stronger sense of innovation, moving beyond the "just enough" paradigm to truly capture the hearts and wallets of a broader consumer base.