Microsoft Defender Under Siege: Threat Actors Exploit Multiple Zero-Day Vulnerabilities for Privilege Escalation and Service Disruption

A critical warning has been issued by cybersecurity firm Huntress, indicating that sophisticated threat actors are actively exploiting a trio of recently revealed security flaws within Microsoft Defender, a ubiquitous endpoint protection solution. These exploits grant attackers elevated privileges on compromised systems, posing a significant threat to countless organizations globally. The vulnerabilities, publicly disclosed as zero-days by a researcher known as Chaotic Eclipse (also identified as Nightmare-Eclipse), underscore the persistent tension between security researchers and software vendors regarding the responsible disclosure process.
The ongoing malicious activity centers around three distinct vulnerabilities, codenamed BlueHammer, RedSun, and UnDefend. All three were made public by Chaotic Eclipse following perceived inadequacies in Microsoft’s handling of the vulnerability disclosure, a move that bypassed the conventional Coordinated Vulnerability Disclosure (CVD) process. While BlueHammer and RedSun are classified as Local Privilege Escalation (LPE) flaws, allowing attackers to gain higher-level access within an already compromised system, UnDefend introduces a critical Denial-of-Service (DoS) condition. This DoS flaw specifically impacts Microsoft Defender’s ability to receive and apply vital definition updates, effectively crippling its protective capabilities and leaving systems exposed to further threats.
Understanding the Core Vulnerabilities and Their Impact
To fully grasp the severity of the current situation, it is crucial to understand the nature of these vulnerabilities:
-
BlueHammer (CVE-2026-33825): This is a Local Privilege Escalation (LPE) vulnerability. In the realm of cybersecurity, an LPE flaw is a severe weakness that allows an attacker, who has already gained initial, low-level access to a system, to elevate their privileges to a higher level, often to that of an administrator or even the system itself. For an attacker, achieving administrative privileges is a pivotal step, as it grants them unfettered control over the compromised machine. This control can be leveraged to disable security software, install persistent backdoors, access sensitive data, modify system configurations, or even move laterally across a network to compromise additional systems. The exploitation of BlueHammer essentially converts a relatively minor breach into a full-scale system takeover, making it an incredibly valuable tool for adversaries. Microsoft has since moved to address BlueHammer as part of its Patch Tuesday updates released earlier this week, tracking it under the CVE identifier CVE-2026-33825.
-
RedSun: Similar to BlueHammer, RedSun is also an LPE flaw impacting Microsoft Defender. While the specific technical nuances differentiating it from BlueHammer have not been extensively detailed in public disclosures, its classification as an LPE vulnerability means it carries the same profound risks. An attacker exploiting RedSun would similarly be able to elevate their privileges from a standard user account to one with administrative or system-level access. This duality of LPE vulnerabilities within the same critical security product amplifies the risk, offering multiple pathways for adversaries to achieve their objectives even if one avenue is patched or mitigated. As of the time of writing, a patch for RedSun has not been publicly released, leaving systems vulnerable to active exploitation.
-
UnDefend: This vulnerability enables a Denial-of-Service (DoS) condition specifically targeting Microsoft Defender’s definition update mechanism. A DoS attack typically aims to make a machine or network resource unavailable to its intended users. In this context, UnDefend is particularly insidious because it targets the very product designed to protect the system. By blocking definition updates, attackers can prevent Microsoft Defender from receiving the latest signatures for malware, zero-day threats, and other malicious activity. This effectively renders the antivirus solution increasingly obsolete and ineffective over time, creating a window of opportunity for attackers to deploy new or polymorphic malware that would otherwise be detected. The inability of an endpoint protection platform to update its threat intelligence is a catastrophic failure, leaving the endpoint largely defenseless. Like RedSun, UnDefend remains unpatched, making it a critical ongoing threat.
The Controversial Disclosure: Chaotic Eclipse and the Zero-Day Dilemma
The release of these vulnerabilities as "zero-days" by the researcher Chaotic Eclipse, also known by the handle Nightmare-Eclipse, has ignited renewed discussions within the cybersecurity community about the delicate balance of vulnerability disclosure. A zero-day vulnerability is a software flaw that is unknown to the vendor (and therefore unpatched) when it is first exploited by attackers. When a researcher publicly discloses such a flaw, especially with proof-of-concept (PoC) code, before a patch is available, it is often referred to as "full disclosure."
Chaotic Eclipse’s decision to release BlueHammer, RedSun, and UnDefend publicly, complete with PoC exploits hosted on GitHub, was explicitly stated as a response to Microsoft’s perceived shortcomings in its vulnerability handling process. This highlights a persistent point of contention between independent security researchers and large software vendors. Researchers often argue that full disclosure, while potentially risky, serves to pressure vendors into swift action and educates the public about imminent threats. Vendors, conversely, strongly advocate for Coordinated Vulnerability Disclosure (CVD), a process where researchers privately report vulnerabilities to the vendor, allowing time for a patch to be developed and deployed before public disclosure. Microsoft’s own MSRC (Microsoft Security Response Center) policy outlines its commitment to CVD, emphasizing the importance of investigating and addressing issues carefully before public disclosure to protect customers.
The tension arises when researchers feel that vendors are not acting quickly enough, are downplaying the severity of findings, or are not adequately compensating researchers for their efforts through bug bounty programs. While full disclosure can force a vendor’s hand, it also immediately puts all users at risk by providing blueprints for exploitation to malicious actors. Chaotic Eclipse’s actions, while controversial, underscore the frustration some researchers experience with the established CVD framework and their belief that public transparency is sometimes necessary to drive change and ensure user safety.
Chronology of Exploitation and Patching Efforts
The timeline of events surrounding these vulnerabilities paints a concerning picture of rapid exploitation following disclosure:
- Prior to April 10, 2026: Chaotic Eclipse publicly discloses the vulnerabilities, including PoC code for BlueHammer, RedSun, and UnDefend.
- April 10, 2026: Huntress observes active exploitation of the BlueHammer vulnerability (CVE-2026-33825) in the wild. This indicates that threat actors quickly weaponized the publicly available PoC.
- Earlier this week (relative to April 17, 2026): Microsoft releases its monthly Patch Tuesday updates. As part of this cycle, a fix for BlueHammer (CVE-2026-33825) is included, addressing one of the three critical flaws.
- April 16, 2026: Huntress detects the weaponization and exploitation of RedSun and UnDefend proof-of-concept exploits in active attacks. This confirms that despite a partial patch from Microsoft, threat actors are still leveraging the unaddressed vulnerabilities.
- April 17, 2026: Huntress publicly issues its warning, detailing the observed in-the-wild exploitation of all three flaws and emphasizing the ongoing risk posed by the unpatched RedSun and UnDefend vulnerabilities.
This rapid sequence, from disclosure to active exploitation, highlights the "race to patch" that organizations face. The mere six-day window between the first observed BlueHammer exploitation and the weaponization of RedSun and UnDefend PoCs demonstrates how quickly sophisticated adversaries can integrate new zero-day exploits into their attack methodologies.

Huntress’s Crucial Observations and Rapid Response
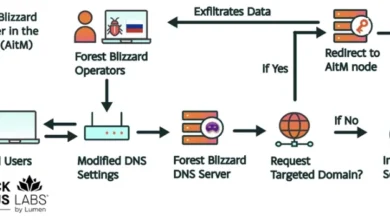
The cybersecurity vendor Huntress has been instrumental in bringing these active exploits to light. Their monitoring and threat hunting capabilities allowed them to identify the malicious activity in compromised environments. In a series of posts shared on X (formerly Twitter), Huntress detailed the specific indicators of compromise (IoCs) and attacker techniques they observed.
The company noted that the exploitation of these vulnerabilities often followed "typical enumeration commands," such as whoami /priv, cmdkey /list, and net group. These commands are standard tools used by attackers after gaining initial access to a system.
whoami /priv: This command is used to determine the privileges associated with the current user account. An attacker would use this to confirm if their LPE exploit was successful and if they now possess elevated rights.cmdkey /list: This command lists stored credentials on a system. Attackers often use it to find cached network credentials that could facilitate lateral movement to other systems.net group: This command is used to enumerate user groups, which can help attackers map out network structure, identify administrative groups, and discover potential targets for further privilege escalation or lateral movement.
The observation of these commands, indicating "hands-on-keyboard threat actor activity," is particularly concerning. "Hands-on-keyboard" signifies that a human attacker is actively interacting with the compromised system, rather than relying solely on automated malware. This suggests a more targeted and adaptable approach, where attackers can respond to defensive measures and make strategic decisions in real-time. This level of engagement often precedes more significant data exfiltration, deployment of ransomware, or long-term persistence within a network.
Upon detecting this activity, Huntress confirmed that it took immediate steps to isolate the affected organization. This rapid incident response is critical in containing the spread of an attack and preventing further post-exploitation activities, such as lateral movement, data exfiltration, or the deployment of destructive payloads.
Microsoft’s Official Stance and Broader Commitment
In response to the unfolding situation, Microsoft confirmed that the BlueHammer exploit had been addressed via CVE-2026-33825. A Microsoft spokesperson reiterated the company’s commitment to security, stating, "Microsoft has a customer commitment to investigate reported security issues and update impacted devices to protect customers as soon as possible."
The spokesperson also emphasized Microsoft’s support for coordinated vulnerability disclosure (CVD), describing it as "a widely adopted industry practice that helps ensure issues are carefully investigated and addressed before public disclosure, supporting both customer protection and the security research community." This statement, while standard, subtly underscores the company’s preference for the CVD model, implicitly contrasting it with the full disclosure approach taken by Chaotic Eclipse. It highlights the vendor’s perspective that a structured disclosure process allows for a more controlled and less disruptive patching cycle, ultimately benefiting the broader user base.
However, the fact that RedSun and UnDefend remain unpatched at the time of writing leaves a significant security gap. While Microsoft’s commitment to investigate and patch is clear, the delay in addressing these critical flaws, especially after public disclosure and observed exploitation, presents a challenge to their security posture and the trust of their users.
Broader Implications for Endpoint Security and Organizations
The exploitation of vulnerabilities in Microsoft Defender, a cornerstone of endpoint security for millions of Windows users globally, carries profound implications:
- Undermining Trust in Core Security Tools: Microsoft Defender is often the primary, and sometimes the only, endpoint protection solution for many businesses and individual users. When such a fundamental security tool is itself compromised, it erodes trust and creates a significant blind spot in an organization’s defenses.
- Gateway to Deeper Compromise: Local Privilege Escalation is a critical step in almost every advanced persistent threat (APT) attack chain. Attackers rarely stop at initial access; they seek to expand their control. LPE vulnerabilities like BlueHammer and RedSun provide the necessary stepping stone for threat actors to move from a limited user account to full administrative control, enabling them to install rootkits, disable other security controls, steal credentials, and exfiltrate sensitive data.
- Evasion of Detection and Persistence: The UnDefend DoS vulnerability, by crippling Defender’s update mechanism, allows attackers to bypass detection for new malware strains. This defensive evasion tactic is highly effective, as it renders the endpoint security product increasingly irrelevant against evolving threats. It also provides a window for attackers to establish persistent access without fear of immediate detection.
- The Patch Management Imperative: The rapid exploitation of these flaws underscores the critical importance of timely patch management. While Microsoft addressed BlueHammer in its Patch Tuesday updates, organizations must have robust processes in place to deploy these patches immediately. The continued unpatched status of RedSun and UnDefend means that even patched systems remain vulnerable to a significant degree.
- The Value of Layered Security and EDR/XDR: This incident powerfully illustrates why relying on a single security solution is insufficient. Even the most robust endpoint protection platforms can have vulnerabilities. This highlights the indispensable role of advanced Endpoint Detection and Response (EDR) and Extended Detection and Response (XDR) solutions. While Defender might have a flaw, an EDR/XDR solution can still detect the behavior of an attacker exploiting that flaw (e.g., the execution of
whoami /privor attempts to disable services). Huntress’s ability to detect the "hands-on-keyboard" activity is a testament to the efficacy of such behavioral monitoring. - Supply Chain Risk: Given the widespread deployment of Microsoft Defender across enterprises, government agencies, and small businesses, vulnerabilities in this product represent a significant supply chain risk. A single flaw can potentially impact an enormous number of interconnected entities.
- Recommendations for Organizations:
- Prioritize Patching: Immediately apply the patch for CVE-2026-33825. Actively monitor for patches for RedSun and UnDefend and apply them as soon as they become available.
- Implement EDR/XDR: Deploy comprehensive EDR or XDR solutions that provide behavioral analysis and threat hunting capabilities beyond signature-based detection. These tools can detect post-exploitation activities even if the initial exploit bypasses the primary endpoint protection.
- Monitor for IoCs: Security teams should actively scan their networks for the enumeration commands and other indicators of compromise mentioned by Huntress.
- Enforce Least Privilege: Limit user privileges to the absolute minimum necessary for their roles. This reduces the impact of an LPE exploit, as even if an attacker gains local admin, their ability to move laterally might still be restricted.
- Network Segmentation: Implement network segmentation to limit the lateral movement capabilities of attackers who have compromised an endpoint.
- Regular Audits and Penetration Testing: Continuously assess the security posture of systems, including endpoint protection configurations and patch compliance.
The Future of Vulnerability Disclosure and Cybersecurity Resilience
This incident serves as a potent reminder of the ongoing, dynamic struggle in cybersecurity. The tension between security researchers, who often push for rapid disclosure, and software vendors, who prefer a controlled patching process, is unlikely to subside. While CVD remains the industry standard, incidents like this demonstrate that when communication breaks down, researchers may resort to full disclosure, placing immediate pressure on both vendors and end-users.
For organizations, the takeaway is clear: a proactive, multi-layered security strategy is non-negotiable. Relying solely on default endpoint protection, even from a major vendor, is no longer sufficient in a landscape where zero-day exploits are quickly weaponized and human adversaries are actively seeking to exploit every weakness. Vigilance, rapid response, and a comprehensive security architecture are paramount to maintaining resilience against an ever-evolving threat landscape.