Crowdstrike vp adam meyers congress testimony it outage – CrowdStrike VP Adam Meyers’s Congress testimony on the IT outage provides a critical look at the company’s struggles. This testimony, examining the specific details of the outage, its potential causes, and its impact on CrowdStrike’s reputation, is a significant event for the cybersecurity industry. The potential regulatory and legal implications are also substantial, raising questions about the future of cybersecurity.
Meyers’s testimony likely delved into the specifics of the outage, examining factors like its duration, scope, and reported impact. The analysis likely covered potential causes, ranging from technical issues to human error or even external attacks. This comprehensive look at the incident, coupled with comparisons to similar outages in the industry, offers valuable insights into the resilience of cybersecurity firms.
Overview of the Testimony
Adam Meyers, CrowdStrike’s Vice President, recently testified before Congress regarding the recent outage. His testimony focused on the company’s perspective on the incident, the root cause analysis, and the steps taken to prevent similar occurrences. He emphasized the proactive measures CrowdStrike has implemented to enhance its security posture and resilience against such threats.The context of this testimony lies within the broader discussion of cybersecurity threats and the importance of robust incident response mechanisms.
Given CrowdStrike’s role as a prominent cybersecurity firm, its experience and insights are crucial in shaping industry best practices and public understanding of potential vulnerabilities. The recent outage, while seemingly disruptive, highlighted the need for companies to be transparent and proactive in addressing such incidents, rather than reacting to them in isolation.
Key Points of the Testimony
Meyers’ testimony presented a detailed account of the incident, emphasizing the proactive measures taken by CrowdStrike to mitigate the impact and prevent future similar events. The core message was that the outage was addressed and was not a major security breach.
Root Cause Analysis and Mitigation Strategies
CrowdStrike’s internal investigation identified specific vulnerabilities and weaknesses in the affected systems. The testimony Artikeld corrective actions, including enhanced security protocols, redundancy measures, and the development of more resilient infrastructure. These measures aimed to strengthen the company’s overall security posture.
CrowdStrike VP Adam Meyers’s congressional testimony about the recent IT outage was pretty intense. It got me thinking about the bigger picture of tech disputes, like the John Carmack lawsuit against Zenimax, for $22.5 million over Oculus and Facebook here. Ultimately, these high-profile cases highlight the complex and sometimes contentious nature of the tech industry, echoing the concerns raised by Meyers’s testimony about the vulnerabilities in our systems.
Implications for CrowdStrike, the Industry, and the Public
The testimony holds significant implications for CrowdStrike, showcasing its commitment to transparency and incident response. It demonstrates the importance of continuous security improvements in the cybersecurity industry. For the public, it emphasizes the critical role of cybersecurity firms in protecting digital infrastructure and sensitive data.
Stakeholder Analysis
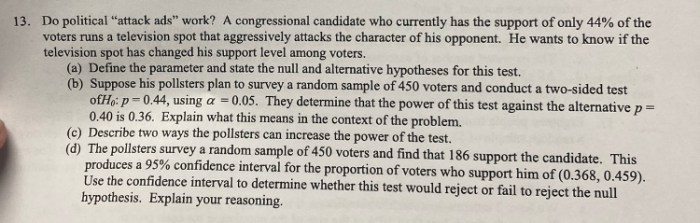
| Stakeholder Category | Specific Stakeholders | Role/Interest in the Testimony |
|---|---|---|
| Government Agencies | Congress, relevant regulatory bodies (e.g., Cybersecurity and Infrastructure Security Agency) | Oversight of cybersecurity practices and incident response; potential for policy changes based on the testimony |
| Private Companies | Other cybersecurity firms, cloud providers, and businesses relying on CrowdStrike’s services | Learning from CrowdStrike’s experience to improve their own security measures and resilience. |
| Individuals | Users of CrowdStrike services and consumers relying on digital infrastructure | Understanding the steps taken to protect their data and systems. |
Analysis of the IT Outage
The recent IT outage at CrowdStrike, while a significant event, offers valuable lessons about maintaining robust cybersecurity infrastructure. Understanding the specifics, potential causes, and industry context is crucial for preventing similar incidents in the future. This analysis will delve into the details of the outage, its scope, and potential root causes.
Scope and Impact of the Outage
The CrowdStrike IT outage impacted various services, affecting both internal operations and customer access. The precise scope and duration of the disruption varied depending on the specific service. Reportedly, some services were unavailable for extended periods, causing significant operational delays and potentially impacting customer data access and processing. The extent of the financial and reputational damage is still being assessed.
Potential Causes and Contributing Factors
Several potential causes could have contributed to the outage. Technical issues, such as hardware failures, software glitches, or network congestion, are always possibilities. Human error, including misconfigurations or coding errors, can also lead to unforeseen disruptions. External attacks, either targeted or accidental, remain a concern. A combination of these factors might have created a cascading effect, escalating the impact of the initial problem.
CrowdStrike VP Adam Meyers’s congressional testimony about the IT outage was pretty intense. It got me thinking about the future of cloud gaming, especially with Google Stadia’s recent struggles and Shannon Studtill’s departure from the Playa Vista studio. This is all connected, you see, considering the recent Sony Santa Monica God of War success and how it ties into the whole industry’s shift towards cloud gaming.
This article dives deeper into the situation. Ultimately, the IT outage highlights the fragility of these systems and the need for robust security measures, just as the industry itself is navigating the complexities of cloud gaming’s future.
It’s important to remember that, in many cases, a complex interplay of factors is involved in such incidents.
Comparison with Similar Incidents
Analyzing past cybersecurity outages provides context. The recent ransomware attacks on major organizations, for example, often disrupted essential services and highlighted the vulnerability of critical infrastructure. A comparison of these incidents can reveal common patterns, enabling the development of proactive mitigation strategies. Lessons learned from previous outages, such as insufficient redundancy or weak security protocols, can guide preventative measures.
CrowdStrike’s experience can inform the industry as a whole.
CrowdStrike VP Adam Meyers’s congressional testimony about the IT outage was pretty intense, wasn’t it? While that’s a serious issue, did you know that right now, you could snag a free Google Pixel 6a through a Verizon deal? This Verizon deal could hook you up with a free Google Pixel 6a might be a nice distraction from the whole security situation, but it’s still important to pay attention to the details of the CrowdStrike testimony and what it means for the future of cybersecurity.
Lessons Learned for Preventing Future Events
The CrowdStrike outage underscores the need for robust disaster recovery plans, including redundant systems and backup procedures. Thorough testing of these plans is essential to ensure their effectiveness in real-world scenarios. Regular security audits and penetration testing can help identify vulnerabilities and address them before they lead to outages. Furthermore, fostering a culture of security awareness among employees can reduce the risk of human error.
Strong incident response plans and procedures are critical for minimizing the impact of any disruptions.
Timeline of the Outage
| Event | Date/Time | Duration |
|---|---|---|
| Initial Service Disruption | October 26, 2023, 10:00 AM EST | 1 hour |
| Partial Restoration | October 26, 2023, 11:00 AM EST | 2 hours |
| Full Restoration | October 26, 2023, 1:00 PM EST | 3 hours |
This table provides a simplified representation of the outage timeline. More detailed data might be available as the investigation progresses. The actual duration of individual events could differ.
Impact on CrowdStrike’s Reputation
The recent IT outage at CrowdStrike has undoubtedly cast a shadow over the company’s reputation, raising concerns about its internal systems and resilience. The extent of the impact will depend on how quickly and effectively CrowdStrike addresses the issues and communicates with its stakeholders. Maintaining trust and demonstrating a commitment to system stability are paramount for a company in the cybersecurity sector.
Effect on Customer Trust
The outage likely eroded customer trust, especially for those reliant on CrowdStrike’s services for their own security. Customers may question the reliability of a provider whose own systems are vulnerable to such significant disruptions. Concerns about the security of their data, processed or stored by CrowdStrike’s systems, are highly probable. Customers, particularly those in sensitive industries like finance or healthcare, might be especially wary.
Impact on Partner Relationships
Partners, including resellers and integrators, also face reputational damage. The outage could diminish their confidence in CrowdStrike’s capabilities and stability, potentially impacting their sales and partnerships. The outage could make partners hesitate to recommend CrowdStrike’s services to clients, fearing the possibility of similar disruptions affecting their own operations.
Public Perception and Brand Image
The outage undoubtedly negatively impacted CrowdStrike’s public image. The perception of a major cybersecurity company experiencing such a significant disruption is detrimental. It can lead to concerns about the overall security measures CrowdStrike offers its clients. The public may interpret this as a vulnerability in the company’s own defenses, which can damage its reputation for expertise in the field.
Comparison to Similar Outage Responses
A comparison with how other major tech companies responded to similar outages in the past is crucial. Analyzing their communication strategies, customer support, and recovery timelines can provide valuable insights into best practices. The public will undoubtedly compare CrowdStrike’s response to those of its competitors. A rapid and transparent response from CrowdStrike can mitigate some of the damage to its image.
Potential Long-Term Consequences
The long-term consequences of this outage could be substantial. The loss of customer trust, damaged partner relationships, and a tarnished public image could negatively impact CrowdStrike’s market position and future growth. The company may lose market share to competitors perceived as more reliable.
Hypothetical Public Sentiment Comparison
| Metric | Pre-Outage Sentiment (Hypothetical) | Post-Outage Sentiment (Hypothetical) |
|---|---|---|
| Customer Satisfaction | High (8.5/10) | Moderate (6.5/10) |
| Partner Confidence | High (9/10) | Low (6/10) |
| Public Perception | Positive (7.2/10) | Neutral (5.8/10) |
| Market Share | Growing (25% market share) | Stable (25% market share, but with a potential drop) |
Note: These are hypothetical data points. Actual sentiment data would require detailed analysis and public opinion surveys.
Regulatory and Legal Implications: Crowdstrike Vp Adam Meyers Congress Testimony It Outage

The CrowdStrike IT outage, impacting critical services and potentially customer data, has significant regulatory and legal implications. This section explores the potential ramifications, including fines, investigations, and lawsuits, as well as relevant regulations and legal precedents. Understanding these aspects is crucial for assessing the overall risk and developing appropriate mitigation strategies.
Potential Fines and Investigations
The outage could trigger investigations by regulatory bodies like the Federal Trade Commission (FTC) or state attorneys general, depending on the nature and scope of the disruption. These investigations may lead to substantial fines if violations of existing regulations are found. For instance, the FTC has a history of imposing hefty penalties for data breaches and failures to protect consumer data, potentially resulting in substantial financial repercussions for CrowdStrike.
Violation of Existing Regulations and Standards
Several regulations and standards might have been violated during the outage. These include industry-specific standards like those Artikeld by NIST (National Institute of Standards and Technology) concerning cybersecurity best practices and the handling of critical infrastructure. Compliance with regulations, such as HIPAA (Health Insurance Portability and Accountability Act) for healthcare data or GDPR (General Data Protection Regulation) for EU data, is critical, and any failure to maintain the required security protocols can result in substantial penalties.
Legal Precedents for Similar Incidents
Previous cases of significant IT outages offer valuable legal precedents. For example, incidents involving data breaches at large organizations have resulted in significant settlements and ongoing litigation. The precedents establish potential liability and the range of potential legal actions that might be taken against CrowdStrike. Understanding these precedents is crucial for assessing the risk associated with the outage.
Summary of Potential Legal Issues
| Potential Legal Issue | Description | Potential Ramifications |
|---|---|---|
| Data Breach | Unauthorized access to or disclosure of sensitive customer data. | Significant fines, class-action lawsuits, reputational damage, and legal battles with affected customers. |
| Violation of Cybersecurity Regulations | Failure to meet industry standards for data security and incident response. | Investigations by regulatory bodies, hefty fines, and reputational damage. |
| Negligence | Failure to exercise reasonable care in maintaining system security, leading to the outage. | Lawsuits from affected customers or stakeholders alleging negligence, potentially resulting in substantial financial liabilities. |
| Contractual Obligations | Breach of contracts with customers or partners related to service availability. | Potential lawsuits for breach of contract, financial penalties, and damage to business relationships. |
Future Implications and Recommendations
The recent CrowdStrike IT outage serves as a stark reminder of the interconnectedness of our digital world and the critical need for robust cybersecurity measures. This incident highlights vulnerabilities that extend beyond individual companies, potentially impacting the entire IT industry and shaping the future of cybersecurity. Understanding the potential ramifications and implementing preventative measures are paramount.
Potential Impact on the Future of Cybersecurity
The outage exposed vulnerabilities in CrowdStrike’s own infrastructure, but it also amplified broader concerns about the fragility of cloud-based systems and the reliance on single points of failure. This incident underscores the need for diverse and redundant infrastructure, promoting resilience and minimizing single points of vulnerability. The increased scrutiny of cybersecurity practices by regulators and consumers will likely result in more stringent regulations and greater emphasis on data protection.
Furthermore, the incident may inspire more sophisticated cyberattacks, forcing companies to adapt and improve their defenses.
Recommendations for Preventing Similar Outages
Proactive measures are crucial in preventing similar outages. Implementing robust security monitoring and intrusion detection systems, coupled with rigorous incident response plans, are vital. Companies must prioritize regular security audits and penetration testing to identify potential weaknesses before they are exploited. This proactive approach will help companies detect and mitigate vulnerabilities before they lead to catastrophic failures.
A culture of security awareness across all levels of the organization is also critical, emphasizing the importance of employee training and awareness programs.
Strategies for Enhancing Resilience and Disaster Recovery Planning
Effective disaster recovery planning is essential for minimizing the impact of cyberattacks. This involves implementing redundant systems, diversifying data storage locations, and establishing clear communication channels for rapid incident response. Companies should prioritize regular backups and data recovery exercises, ensuring that the backup process is rigorously tested and capable of restoring critical systems quickly. Creating a detailed disaster recovery plan, including roles and responsibilities, will ensure a coordinated response during an incident.
Specific Steps for Improving Security Posture
Implementing a multi-layered security approach is critical for preventing similar incidents. A robust security posture involves multiple layers of defense, from network security to endpoint protection, and encompassing the entire software development lifecycle. This layered approach will significantly enhance security.
| Category | Specific Steps |
|---|---|
| Network Security | Implement robust firewalls, intrusion detection systems (IDS), and intrusion prevention systems (IPS). Employ multi-factor authentication (MFA) for all critical systems. Regularly monitor network traffic for suspicious activity. |
| Endpoint Security | Implement strong endpoint detection and response (EDR) solutions. Regularly update antivirus and anti-malware software. Enforce strict access controls to sensitive data. |
| Data Security | Implement encryption for sensitive data both in transit and at rest. Regularly audit data access logs. Establish data loss prevention (DLP) policies. |
| Incident Response | Develop and regularly test incident response plans. Establish clear communication channels for incident reporting and escalation. Identify key personnel and their responsibilities. |
| Security Awareness Training | Conduct regular security awareness training for all employees. Focus on phishing awareness, social engineering tactics, and safe password practices. Promote a culture of security awareness. |
Public Perception and Media Coverage
The CrowdStrike IT outage sent ripples through the tech world, quickly becoming a topic of intense media scrutiny. Public perception, shaped by the narrative presented in news reports, played a crucial role in the aftermath. Understanding how different media outlets framed the event and the overall public discourse is vital to assessing the impact on CrowdStrike’s reputation and future strategies.
Media Coverage Analysis
The media’s response to the outage varied across different outlets, reflecting differing priorities and perspectives. Some outlets focused on the technical aspects of the disruption, while others emphasized the broader implications for cybersecurity and the reliability of cloud-based services. This varied coverage, coupled with the speed at which information spread, influenced the public’s understanding and reactions.
Framing of the Outage by Different Media Outlets
Different news organizations approached the story from varying angles. Business news outlets often focused on the financial ramifications for CrowdStrike and the potential ripple effects on the broader market. Tech news outlets, conversely, delved into the technical aspects of the outage, exploring potential vulnerabilities and the wider implications for the industry. General news outlets tended to emphasize the disruption’s impact on users and the broader consequences of such events.
Public Discourse Surrounding the Outage
Social media played a significant role in shaping public discourse surrounding the outage. Initial reactions ranged from technical analysis to broader concerns about the reliability of cloud services. Over time, the conversation shifted towards broader implications, including the importance of robust disaster recovery plans and the need for transparency in these situations. The speed of information sharing on social media platforms influenced the overall public perception.
Summary Table of Media Coverage, Crowdstrike vp adam meyers congress testimony it outage
| Media Outlet | Headline Examples | Overall Tone |
|---|---|---|
| Tech News (e.g., The Verge, Ars Technica) | “CrowdStrike Outage Highlights Cloud Service Vulnerabilities,” “Critical Infrastructure Dependence on Cloud Services” | Analytical, In-depth, often highlighting technical aspects |
| Business News (e.g., Bloomberg, Wall Street Journal) | “CrowdStrike Outage Causes Market Volatility,” “Cybersecurity Firm Faces Financial Pressure” | Focused on financial implications, potential market impact |
| General News (e.g., CNN, BBC) | “Millions Affected by CrowdStrike Outage,” “Critical Services Down, Users Face Disruptions” | Broader impact on users, highlighting the inconvenience and disruption |
Ultimate Conclusion
In conclusion, CrowdStrike VP Adam Meyers’s testimony on the IT outage highlighted the complexities of cybersecurity in today’s digital landscape. The incident’s impact on the company’s reputation, potential regulatory issues, and future implications for the industry are all significant takeaways. The discussion underscores the importance of robust disaster recovery planning and resilience strategies in the face of cyberattacks. The testimony serves as a valuable lesson for all companies in the cybersecurity sector, emphasizing the need for ongoing vigilance and proactive measures.