Financially Motivated Cybercrime Group TeamPCP Unleashes Data-Wiping Worm Targeting Iranian Systems Amidst Escalating Global Cyber Conflict
A sophisticated and financially driven data theft and extortion collective, known as TeamPCP, has intensified its operations by deploying a destructive worm specifically designed to target systems within Iran. This new malicious payload, identified as a wiper, propagates through inadequately secured cloud services and systematically erases data on infected machines that are configured with Iran’s time zone or have Farsi set as their default language. The emergence of this Iran-specific targeting marks a notable escalation in the group’s activities, blending its established financial motivations with a seemingly geopolitically tinged destructive capability.
The Rise of TeamPCP: A Cloud-Native Threat
Cybersecurity experts began tracking the activities of TeamPCP in December 2025, identifying it as a relatively nascent but highly effective cybercrime group. Unlike many traditional threat actors that primarily focus on exploiting end-user devices, TeamPCP has distinguished itself by weaponizing exposed control planes and predominantly targeting cloud infrastructure. Their campaigns initially focused on compromising corporate cloud environments by leveraging a self-propagating worm. This worm specifically sought out and exploited vulnerabilities in exposed Docker APIs, Kubernetes clusters, Redis servers, and the notorious React2Shell vulnerability. Once access was gained, TeamPCP’s standard operating procedure involved moving laterally through victim networks, siphoning authentication credentials, and subsequently extorting victims, typically via the Telegram messaging platform.
The group’s strategy, as highlighted by security firm Flare in a January profile, is not rooted in developing novel exploits or groundbreaking malware. Instead, TeamPCP’s strength lies in its large-scale automation and seamless integration of well-known attack techniques. Assaf Morag of Flare articulated this, stating, "TeamPCP’s strength does not come from novel exploits or original malware, but from the large-scale automation and integration of well-known attack techniques." He further elaborated that the group "industrializes existing vulnerabilities, misconfigurations, and recycled tooling into a cloud-native exploitation platform that turns exposed infrastructure into a self-propagating criminal ecosystem." This approach has proven highly effective, with Flare’s analysis indicating that Azure (61%) and AWS (36%) servers collectively account for a staggering 97% of the compromised cloud infrastructure attributed to TeamPCP. This concentration underscores the group’s specific focus on major cloud providers, which offer a vast attack surface if not properly secured.
The "CanisterWorm" and its Iranian Target
The wiper campaign against Iranian targets materialized this past weekend, demonstrating a clear and concerning shift in TeamPCP’s operational focus. Security researcher Charlie Eriksen from Aikido, a cybersecurity firm, was instrumental in identifying and analyzing this new payload. In a blog post published on Sunday, Eriksen detailed how the same technical infrastructure previously utilized by TeamPCP in earlier attacks was repurposed to deploy this destructive new malware.
Aikido has dubbed this malicious infrastructure "CanisterWorm," a name derived from the group’s orchestration method. TeamPCP leverages an Internet Computer Protocol (ICP) canister, a system composed of tamperproof, blockchain-based "smart contracts" that encapsulate both code and data. These ICP canisters possess several characteristics that make them attractive to threat actors: they can serve web content directly, their distributed architecture renders them highly resistant to takedown attempts, and they remain operational as long as their operators continue to pay virtual currency fees. This resilience provides TeamPCP with a robust and persistent platform for launching its campaigns.
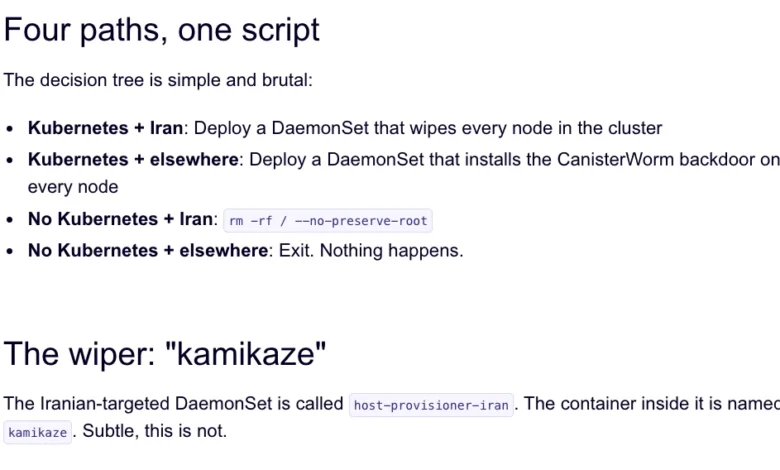
The CanisterWorm’s operational logic is particularly insidious. Upon infection, it performs a check: if the victim system’s timezone and locale settings correspond to Iran, the wiper component activates. Eriksen elaborated on its destructive potential, explaining that "if the wiper component detects that the victim is in Iran and has access to a Kubernetes cluster, it will destroy data on every node in that cluster." In scenarios where a Kubernetes cluster is not detected, the malware will simply wipe data from the local machine. This targeted destruction, combined with the group’s prior financially motivated activities, raises questions about the evolving motivations of TeamPCP, suggesting a potential desire for notoriety or disruption beyond mere monetary gain.
A String of Supply Chain Breaches: Trivy and KICS
The deployment of the Iran-targeted wiper follows a series of high-profile supply chain attacks executed by TeamPCP, highlighting a broader vulnerability in the software development ecosystem. On March 19, TeamPCP launched a significant supply chain attack against Trivy, a popular vulnerability scanner developed by Aqua Security. The attackers managed to inject credential-stealing malware into official releases hosted on GitHub Actions, a widely used platform for automating software development workflows.
Aqua Security swiftly responded by removing the malicious files, but the damage had already been done. Cybersecurity firm Wiz reported that the attackers successfully published malicious versions of Trivy, which were capable of exfiltrating sensitive data including SSH keys, cloud credentials, Kubernetes tokens, and even cryptocurrency wallets from affected users. This incident underscored the critical risk posed by compromised software development tools and repositories, as a single breach can cascade down to affect numerous downstream users and organizations.
The threat actors’ audacity was further demonstrated on March 23, when Wiz reported that TeamPCP had also pushed credential-stealing malware to the GitHub Action for KICS, another vulnerability scanner developed by Checkmarx. The compromise of KICS’s GitHub Action occurred between 12:58 and 16:50 UTC on that day, indicating a continued, aggressive campaign to exploit trusted software supply chains. These repeated attacks on essential security tools illustrate TeamPCP’s sophisticated understanding of the software development lifecycle and its choke points.

GitHub’s Growing Malware Problem and TeamPCP’s Tactics
The recent incidents involving TeamPCP have cast a harsh spotlight on the increasing prevalence of malware within the GitHub ecosystem. As Catalin Cimpanu, a reporter for Risky Business, noted in his newsletter "GitHub is Starting to Have a Real Malware Problem," supply chain attacks have seen a marked increase since 2024, as threat actors recognize the efficiency and widespread impact they can achieve. GitHub, as the world’s largest platform for software development, becomes an attractive target due to its centrality in the modern software supply chain.
TeamPCP’s operational tactics extend beyond mere injection. Charlie Eriksen observed the group’s penchant for bragging about their exploits in a Telegram group, claiming to have stolen vast amounts of sensitive data from major companies, including a large multinational pharmaceutical firm. Furthermore, after compromising Aqua Security a second time, TeamPCP reportedly took control of numerous GitHub accounts and began "spamming these with junk messages." This behavior, Eriksen suggested, was "almost like they were just showing off how much access they had," implying that the visible compromises might be "a small sample of what they have."
This "spamming" tactic also serves a more strategic purpose. Security experts believe that pushing meaningless commits or leveraging services that sell GitHub stars and "likes" can help malicious code packages remain prominent in GitHub search results. This ensures that their tainted software has a higher chance of being discovered and adopted by unsuspecting developers, perpetuating the supply chain compromise. The challenge for GitHub’s security team is formidable, given the platform’s design for copying and creating new versions of projects. As Cimpanu aptly put it, "spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix."
The weekend’s outbreak was not the first time Trivy had been impacted by a supply chain attack. In late February, Trivy was affected by "HackerBot-Claw," an automated threat that mass-exploited misconfigured workflows in GitHub Actions to steal authentication tokens. Eriksen suggested that TeamPCP likely leveraged access gained during this initial compromise of Aqua Security to perpetrate the more recent attacks.
The "Chaotic Evil" Persona and Unpredictable Operations
TeamPCP’s activities are characterized by an erratic and seemingly theatrical operational style. Eriksen noted the group’s tendency to take their malicious code "up and down, rapidly changing it adding new features." In some instances, when the malicious ICP canister wasn’t serving malware downloads, it was observed redirecting visitors to a "Rick Roll" video on YouTube. This unpredictable behavior, coupled with their boasts and public "showing off," led Eriksen to describe TeamPCP’s persona as "Chaotic Evil."
This blend of sophisticated technical capability, financial motivation, and seemingly performative or disruptive actions makes TeamPCP a particularly challenging adversary. The inclusion of an Iran-targeted wiper, despite the group’s primary financial objectives, further complicates the analysis of their ultimate goals. While Eriksen acknowledged the possibility that "this whole Iran thing is just their way of getting attention," it nevertheless introduces a potentially destabilizing element into the already volatile geopolitical landscape. Whether this targeted destruction is a one-off stunt for notoriety or a precursor to more sustained, politically motivated cyber warfare from a financially driven group remains to be seen.
Broader Implications and The Imperative for Enhanced Security
The actions of TeamPCP underscore several critical trends in the contemporary cybersecurity landscape. Firstly, the blurring lines between financially motivated cybercrime and politically or geopolitically tinged attacks represent a significant challenge for attribution and defense. Groups initially driven by profit may, for various reasons, pivot to or incorporate disruptive and destructive elements that align with broader geopolitical tensions.
Secondly, the relentless focus on cloud infrastructure and supply chain vulnerabilities by groups like TeamPCP highlights the urgent need for organizations to re-evaluate and fortify their security postures in these critical areas. Cloud security is no longer merely about perimeter defense; it encompasses robust API security, continuous monitoring of Kubernetes clusters, secure configuration management, and vigilant oversight of development pipelines and third-party software components. The statistic that 97% of TeamPCP’s compromised servers were on Azure and AWS serves as a stark reminder of the attractiveness of these platforms for attackers if not adequately protected.
Thirdly, the incidents involving Trivy and KICS serve as a wake-up call for the open-source software community and platforms like GitHub. While security firms like Aikido, Flare, and Wiz are doing commendable work in spotting these attacks, the sheer scale and decentralized nature of open-source development make it an inherently complex environment to secure. The onus is not solely on developers to maintain secure coding practices but also on platform providers to implement more robust security mechanisms that can proactively detect and mitigate the injection of malicious code into popular repositories and development workflows.
As TeamPCP continues to evolve its tactics, rapidly changing payloads and exploiting new vulnerabilities, the emphasis on real-time threat intelligence, proactive defense, and collaborative information sharing among security researchers, vendors, and platform providers becomes paramount. The "Chaotic Evil" nature of TeamPCP suggests that their next move will likely be as unpredictable as it is destructive, demanding a flexible and resilient response from the global cybersecurity community. The incident serves as a potent reminder that in the interconnected digital world, even financially motivated actors can wield tools capable of significant geopolitical impact.