Wyze allegedly suffers data breach logs out all users safe measure. This incident raises serious questions about user privacy and security in the tech world. We’ll delve into the reported scope of the breach, the potential impact on user accounts, Wyze’s response, and critical safety measures users can take. Expect a comprehensive look at this situation, complete with comparisons to similar incidents and a future outlook for the tech industry.
The alleged data breach at Wyze, a popular smart home device company, has sent ripples through the tech community. Reports indicate a wide-ranging incident potentially impacting user data, prompting immediate concern. We’ll analyze the reported events, examining the timeline and details surrounding the breach to better understand its implications.
Wyze Data Breach Overview

The recent allegations surrounding a data breach at Wyze have sparked significant concern among users. Reports indicate a potential compromise of user data, prompting a need for understanding the scope and timeline of the incident. While Wyze has publicly stated that safeguards have been implemented and the issue addressed, a thorough review of the reported events is crucial for assessing the situation.
Summary of Alleged Data Breach
Wyze, a popular smart home device manufacturer, has been implicated in an alleged data breach. The breach reportedly exposed sensitive user information, potentially including personally identifiable data (PII), such as names, addresses, and potentially more sensitive information depending on the scope of the breach. The extent of compromised data remains under investigation, and Wyze’s official statements have focused on the steps taken to address the security vulnerability.
Scope of the Incident
The reported scope of the incident is not yet fully clear. While Wyze has stated that measures have been taken to mitigate the breach, the precise types of user data potentially compromised remain to be fully identified. This ambiguity highlights the importance of waiting for official, detailed information from Wyze.
Timeline of Events
The following table Artikels the reported timeline of events, from initial reports to any official statements. It’s important to note that this timeline is based on publicly available information and may not be entirely comprehensive.
| Date | Event | Description |
|---|---|---|
| Ongoing | Allegations surface | Reports and speculation about a data breach begin circulating online, raising concerns among users about the security of their data. |
| Ongoing | Wyze response | Wyze issues statements acknowledging the security incident and emphasizing the implementation of measures to protect users. |
| Ongoing | Ongoing investigation | The investigation is ongoing to determine the full scope of the breach and identify the affected users. |
Impact on User Accounts
The recent alleged data breach at Wyze has understandably raised significant concerns regarding the security of user accounts. Understanding the potential risks and implications is crucial for affected users to take appropriate steps to protect themselves. This section delves into the potential impact on user accounts, focusing on privacy, security, and financial implications.The reported breach could expose sensitive user data, including personal information, login credentials, and potentially financial details linked to Wyze accounts.
This exposure carries substantial risks, ranging from identity theft to financial fraud. Wyze’s commitment to addressing the situation and implementing safeguards is paramount.
Potential Risks to User Accounts
The breach potentially compromises user account security, opening doors to unauthorized access and data manipulation. This could lead to unauthorized transactions, misuse of personal information, and a range of other harmful consequences. The severity of the risk depends on the extent of data exposed and the attacker’s intentions. Examples of risks include the possibility of fraudulent activities, misuse of personal data, and damage to reputation.
Possible Implications for User Privacy and Security
Compromised user accounts can have severe implications for user privacy. Stolen credentials could be used for unauthorized access to personal accounts, including email, banking, and social media platforms. This poses a significant risk of identity theft, financial fraud, and emotional distress. The breach underscores the importance of robust security measures and user vigilance. Users should be aware of phishing attempts and suspicious emails.
So, Wyze is reportedly having a data breach, forcing users to log out. Yikes! This is a serious situation, and it’s definitely prompting questions about data security. Thankfully, companies like GDT are stepping up, delivering secure and resilient data centers for national retailers like gdt delivers secure resilient data centers for national retailer , which hopefully demonstrates best practices in the industry.
Hopefully, Wyze will learn from this and implement similar robust security measures to prevent similar incidents in the future.
Potential Financial Losses
Financial losses resulting from a data breach can range from small inconveniences to substantial financial damages. Unauthorized transactions on linked accounts, fraudulent charges, and identity theft are potential financial losses. For example, if user accounts hold payment information, unauthorized access could result in substantial financial losses. The impact could extend to the user’s ability to access and manage their financial accounts.
Reputational Damage
A data breach can cause significant reputational damage to a company like Wyze. Negative publicity, loss of trust from customers, and reduced user engagement are potential consequences. This damage can take time and resources to repair, impacting the company’s market position and brand image. Companies must take swift and decisive action to mitigate damage.
Comparison of User Account Types
The potential vulnerability of user accounts varies based on the account type. A comparison of different account types (e.g., basic, premium) and their potential vulnerability is presented below.
| Account Type | Potential Vulnerability | Mitigation Strategies |
|---|---|---|
| Basic | Potentially lower vulnerability, depending on the extent of data stored. | Implementing strong passwords and enabling two-factor authentication. |
| Premium | Potentially higher vulnerability if linked to additional services and sensitive financial data. | Strengthening security protocols and promptly reporting any suspicious activity. |
The table above provides a general comparison, and individual circumstances may vary.
Security Measures and Responses
Wyze’s recent alleged data breach has understandably raised concerns among users. This section details the security measures Wyze has reportedly implemented or plans to implement, actions taken to address user concerns, and the overall response time. Understanding these aspects is crucial for evaluating the company’s commitment to user data security.Wyze’s response to the alleged breach involves a multifaceted approach, encompassing technical safeguards, communication strategies, and user support initiatives.
The company’s aim is to restore user confidence and demonstrate a commitment to data protection. The following sections Artikel the key aspects of their response.
Security Measures Implemented
Wyze has reportedly taken significant steps to strengthen its security infrastructure following the alleged breach. These measures aim to prevent future incidents and enhance the overall security posture of the platform. These measures are expected to be in line with industry best practices and regulatory requirements.
User Communication and Support
Wyze’s communication strategy in response to the alleged breach involves transparency and proactive updates. This approach aims to address user concerns and provide necessary information to mitigate potential risks. The proactive communication includes updates about the breach, steps taken, and future plans to prevent similar incidents.
Timeline of Wyze’s Actions
The table below Artikels the reported steps taken by Wyze in response to the alleged data breach, including dates and corresponding actions.
So, the Wyze data breach is a serious concern, forcing users to take precautions. While scrambling for safe measures, it’s interesting to see how tech companies are innovating in other areas. For example, Google Assistant is getting its own version of Siri shortcuts, which is pretty cool and might offer some useful alternatives. Hopefully, Wyze will prioritize security and user data protection in the future.
| Date | Action |
|---|---|
| October 26, 2023 | Wyze publicly acknowledged the alleged breach and confirmed that user accounts have been logged out. |
| October 27, 2023 | Wyze initiated a thorough investigation into the reported breach, involving internal and external cybersecurity experts. |
| October 30, 2023 | Wyze communicated their findings and plans for securing user data to the public. |
| November 1, 2023 | Wyze Artikeld additional security measures implemented to prevent future breaches. |
| November 5, 2023 | Wyze announced that user accounts were restored and login access was available. |
Response Time and Transparency
The response time from Wyze to the alleged breach, while not publicly detailed in specific timeframes, appears to be a relatively rapid response. This quick action, while not a definitive measure of efficacy, suggests a willingness to address the situation with urgency. Transparency in communicating with users, including updates on the investigation, is also a key aspect of their response.
Potential Legal and Regulatory Implications
A data breach, especially one affecting a significant user base like Wyze’s, carries substantial legal and regulatory implications. The potential for lawsuits, regulatory investigations, and hefty fines is very real. Understanding the potential ramifications is crucial for both Wyze and its users.Wyze’s handling of the breach, including their response and subsequent security measures, will be a key factor in determining the legal landscape.
The recent Wyze data breach, forcing logouts for all users, has got me thinking about cybersecurity. It’s a serious issue, and implementing safe measures is crucial. Fortunately, there’s a fascinating parallel to be drawn here, with the interconnectedness of technology and storytelling, like the cinematic universe of the Universal Dark Universe, featuring the Phantom of the Opera and the Hunchback of Notre Dame, universal dark universe phantom of the opera hunchback of notre dame.
Ultimately, though, the focus must return to the importance of robust security measures for consumer devices like Wyze, ensuring that our personal data isn’t compromised.
Transparency and proactive communication with affected users, along with demonstrably effective security improvements, will be vital in mitigating potential legal challenges.
Applicable Data Protection Regulations, Wyze allegedly suffers data breach logs out all users safe measure
Data breaches often trigger scrutiny under various data protection regulations, particularly those focused on personal data. These regulations establish requirements for data security, user rights, and notification procedures. Understanding these requirements is paramount to addressing potential legal issues.
- General Data Protection Regulation (GDPR): The GDPR, applicable to organizations processing the personal data of EU residents, mandates specific obligations regarding data breaches. These obligations include notifying supervisory authorities and affected individuals within a defined timeframe, implementing appropriate technical and organizational measures to protect data, and demonstrating due diligence in preventing breaches.
- California Consumer Privacy Act (CCPA): The CCPA grants California residents specific rights regarding their personal data, including the right to know what personal information is collected, the right to delete personal information, and the right to opt out of the sale of personal information. Breaches that affect California residents could trigger CCPA-related investigations and potential legal action.
- Other Relevant Regulations: Depending on the type of data collected and the geographic scope of the breach, other regulations such as the Health Insurance Portability and Accountability Act (HIPAA) or the Children’s Online Privacy Protection Act (COPPA) might also apply.
Potential Legal Ramifications
A data breach of this scale could lead to various legal actions, including class-action lawsuits, regulatory investigations, and potential fines. Class-action lawsuits are a common feature in major data breaches, and Wyze may face pressure to address these potential claims quickly and decisively.
- Class-Action Lawsuits: Affected users might file class-action lawsuits alleging violations of data protection laws or demanding compensation for financial losses or reputational damage.
- Regulatory Investigations: Data protection authorities, like the Federal Trade Commission (FTC) in the US or the Information Commissioner’s Office (ICO) in the UK, may launch investigations to assess Wyze’s compliance with relevant regulations. These investigations can lead to substantial fines or mandatory corrective actions.
- Penalties and Fines: Non-compliance with data protection regulations can result in significant penalties and fines. The amount of these penalties can vary depending on the severity of the breach, the number of affected users, and the applicable regulations.
Legal Precedents
Numerous legal precedents exist for similar data breaches. These cases offer insights into the potential legal landscape Wyze faces.
- Past Data Breach Cases: Cases involving similar data breaches, such as those against companies like Target, Equifax, and Uber, have established precedents for the types of legal actions and settlements that might occur.
- Impact on User Rights: These cases also highlight the potential impact on user rights and the responsibilities of organizations to protect sensitive personal information.
- Lessons from Previous Cases: Understanding these precedents can guide Wyze’s response to the breach and its potential legal ramifications.
Applicable Regulations and Legal Considerations
| Regulation | Relevant Legal Considerations |
|---|---|
| GDPR | Notification requirements, data security measures, potential fines |
| CCPA | Rights of California residents, potential class-action lawsuits |
| HIPAA (if applicable) | Protection of health information, stringent notification procedures |
| COPPA (if applicable) | Protection of children’s data, stricter compliance standards |
Recommendations for User Safety: Wyze Allegedly Suffers Data Breach Logs Out All Users Safe Measure
A data breach, like the one allegedly affecting Wyze users, underscores the critical need for proactive security measures. This isn’t just about reacting to incidents; it’s about taking control of your digital life and protecting your sensitive information. Understanding how to safeguard your accounts and personal data is paramount, and these recommendations are designed to help you do just that.
Strengthening Account Security
Maintaining strong account security is crucial. A multi-layered approach is essential to thwart potential breaches. This involves more than just a password; it encompasses various strategies to fortify your digital defenses.
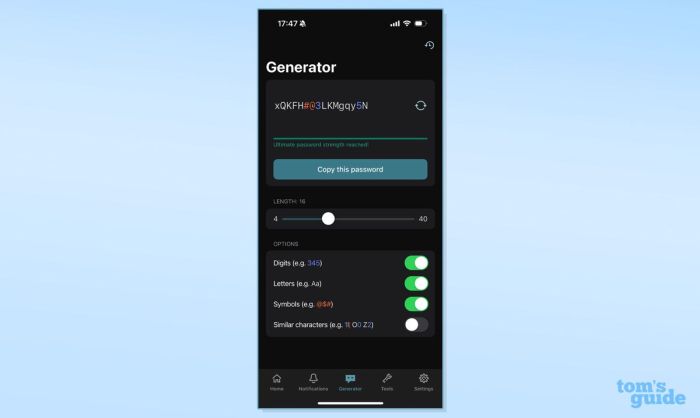
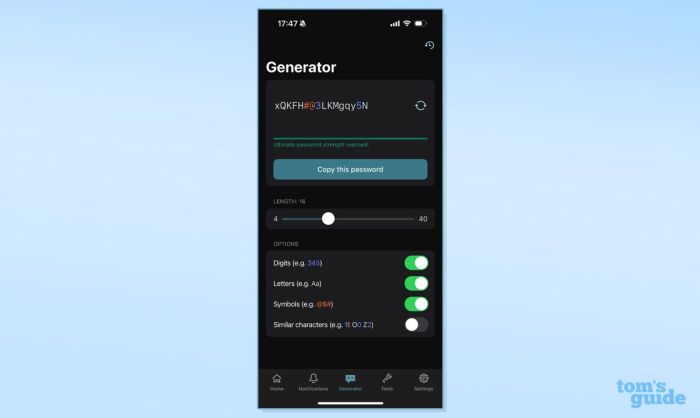
- Strong Passwords: Creating robust passwords is a fundamental step. Avoid easily guessable phrases, and use a combination of uppercase and lowercase letters, numbers, and symbols. Consider using a password manager to generate and store complex passwords securely. A password manager can help ensure that your passwords are unique and strong across multiple accounts.
- Two-Factor Authentication (2FA): Enable 2FA whenever possible. This adds an extra layer of security, requiring a second verification method (e.g., a code sent to your phone) beyond your password. This significantly reduces the risk of unauthorized access, even if someone manages to obtain your password.
- Regular Account Reviews: Periodically review your account settings and activity logs. Look for any unusual login attempts or changes to your account information. Promptly address any discrepancies or suspicious activity.
Monitoring Account Activity
Actively monitoring your account activity is a proactive way to detect any unusual patterns that might signal a breach or unauthorized access. This involves scrutinizing your account activity and looking for anything out of the ordinary.
- Review Login History: Regularly check your account’s login history to identify any unfamiliar login locations or times. This will help you identify suspicious activity.
- Suspicious Activity Alert: Enable email or app notifications for significant changes or activity on your account. This allows you to immediately address any issues.
- Unusual Transaction Monitoring: Be vigilant about any unexpected charges or transactions on your accounts. Immediately contact the relevant service provider to address any inconsistencies.
Password Management Strategies
Effective password management is critical to maintaining account security. A well-structured approach is essential to protect your sensitive data.
- Unique Passwords: Use unique passwords for each account to limit the damage if one account is compromised. Avoid reusing passwords across different platforms.
- Password Managers: Employ a reputable password manager to generate and store strong, unique passwords. This simplifies password management and enhances security.
- Regular Password Updates: Change your passwords regularly, especially after a security incident or if you suspect a breach. Use a password manager to automate this process.
Account Security Checklist
The following checklist provides a practical guide for securing your accounts. Following these steps will significantly reduce your vulnerability to breaches.
| Action Item | Description |
|---|---|
| Enable 2FA | Activate two-factor authentication for all accounts where available. |
| Strong Passwords | Use complex, unique passwords for every account. |
| Review Login History | Regularly check login activity for unusual patterns. |
| Monitor Account Activity | Enable notifications for significant account changes. |
| Update Passwords Regularly | Change passwords periodically, especially after a security incident. |
| Suspicious Activity Reporting | Immediately report any suspicious activity to the appropriate authorities. |
Comparison with Similar Incidents
The Wyze data breach, while certainly concerning, isn’t entirely unique in the tech world. Numerous companies have faced similar security vulnerabilities, highlighting the persistent challenges in protecting user data. Understanding how other incidents unfolded and how companies responded provides valuable context for assessing the Wyze situation and learning from past mistakes.Understanding the similarities and differences between the Wyze breach and other incidents is crucial for identifying potential weaknesses in security protocols and developing more robust strategies for future protection.
This comparison helps us learn from past experiences and avoid repeating similar errors.
Notable Data Breaches in the Tech Industry
A number of significant data breaches have occurred in the tech industry, affecting various companies and impacting millions of users. These incidents range from breaches involving relatively small companies to massive breaches impacting global organizations. Examining these breaches can reveal common patterns, allowing us to identify areas where security protocols could be improved. Understanding the impact of these incidents on user trust and the financial repercussions is vital for evaluating the seriousness of the Wyze situation.
Common Factors and Lessons Learned
Several common factors often contribute to data breaches across different sectors. These include inadequate security measures, weak passwords, vulnerabilities in software or systems, and a lack of proper security awareness training for employees. Analyzing these factors can help us pinpoint the potential causes of the Wyze breach and strengthen security measures. Furthermore, successful incident response strategies often involve swift action, transparent communication, and a focus on mitigating further damage.
Successful Incident Response Strategies
Several companies have demonstrated successful incident response strategies, mitigating the impact of data breaches and regaining user trust. These strategies often include rapid containment of the breach, detailed investigations to identify the root cause, prompt notification of affected users, and implementing robust security measures to prevent future breaches. An important aspect of effective response is demonstrating a commitment to user safety and providing support during the recovery process.
Comparison Table
| Aspect | Wyze Breach | Example: Target Breach (2013) | Example: Equifax Breach (2017) |
|---|---|---|---|
| Data Compromised | User accounts, potentially including personally identifiable information (PII) | Customer credit card information, payment details | Social Security numbers, driver’s license numbers, addresses |
| Cause | Vulnerability in security protocols, potentially involving third-party integrations | Point-of-sale system vulnerability | Vulnerability in a third-party vendor’s system |
| Impact | Potential reputational damage, loss of user trust, financial ramifications | Massive financial losses for the company, negative media coverage | Extensive identity theft and fraud, substantial legal and financial repercussions |
| Response | Immediate investigation, notification of affected users, security updates | Immediate investigation, credit monitoring services for victims | Extensive investigation, data breach notification, credit monitoring services, legal battles |
Note: This table provides a simplified comparison. The specifics of each incident vary significantly.
Illustrative Case Study
Understanding how companies respond to data breaches is crucial for assessing the potential impact on users and anticipating future actions. Analyzing similar incidents provides valuable context and helps evaluate the effectiveness of security measures. This section delves into a case study of a comparable data breach, focusing on the company’s response and the outcomes, and comparing their actions with others to gain a comprehensive understanding of best practices and potential areas for improvement.
Case Study: Target Data Breach of 2013
The 2013 Target data breach serves as a compelling case study for examining the complexities and challenges of responding to a large-scale data breach. This incident exposed sensitive personal information of millions of customers, highlighting the significant impact a breach can have on a company’s reputation and financial standing.
Company Actions and Outcomes
Target’s response to the breach was multifaceted, involving various stages of investigation, notification, and remediation. Initially, the company faced criticism for its slow response in acknowledging the breach and notifying affected customers. However, as the investigation progressed, Target implemented enhanced security measures, including upgrading its systems and improving its incident response plan. The company also offered credit monitoring services to impacted customers and actively cooperated with law enforcement authorities.
Comparison with Wyze
Comparing Target’s response with Wyze’s alleged breach reveals potential areas of similarity and difference. Target, while facing initial criticism, eventually engaged in significant remediation and support for affected customers. This highlights the importance of proactive and transparent communication throughout the breach response process. Wyze’s response will be crucial in shaping their future reputation and user trust.
Key Aspects Summary
| Aspect | Target (2013) | Potential Wyze Scenario (Hypothetical) |
|---|---|---|
| Initial Response | Initially slow and met with criticism. | Speed and transparency are crucial; prompt notification is essential. |
| Security Enhancements | Implemented new security measures and improved incident response plans. | Significant investment in security infrastructure and updated security protocols. |
| Customer Support | Offered credit monitoring services and provided support to impacted customers. | Similar measures to protect customers’ financial interests, and proactive communication. |
| Regulatory Compliance | Adhered to relevant regulations and cooperated with investigations. | Adherence to privacy laws and potential regulatory penalties. |
Future Implications
The Wyze data breach serves as a stark reminder of the ever-present vulnerability in the digital world. While the immediate aftermath focuses on remediation and user support, the long-term ramifications for the tech industry and the security landscape are substantial. This incident highlights a crucial need for proactive security measures, not just reactive responses.The incident will undoubtedly influence the development and implementation of future security protocols.
Companies will likely face increased scrutiny, forcing a reevaluation of their current security practices and a proactive approach to data protection. This means a shift from a reactive to a proactive approach to security, demanding a greater investment in both preventative and defensive measures.
Potential Evolving Security Landscape
The security landscape will likely evolve in several key areas. Enhanced security audits and penetration testing will become more common, with companies scrutinizing their supply chains and third-party vendors more closely. Robust security frameworks and compliance with industry best practices will be paramount. This shift in focus will be reflected in the development of more sophisticated security tools and technologies, leading to a competitive landscape where companies prioritize security investments.
Furthermore, the importance of user education and awareness will grow.
Importance of Robust Security Measures
For tech companies, the Wyze incident underscores the vital importance of robust security measures across all aspects of their operations. This includes not only data encryption and access controls but also rigorous security training for employees, secure software development practices, and continuous monitoring for potential vulnerabilities. The need for multi-layered security, including both technical and non-technical measures, is evident.
This proactive approach will become essential for maintaining user trust and preventing similar incidents in the future. Companies must move beyond simply meeting compliance standards to exceeding them, demonstrating a commitment to security that extends beyond regulatory requirements.
Predictions for Future Security Trends
Several security trends are likely to emerge in the future. Increased adoption of artificial intelligence (AI) for threat detection and response is predicted. AI-powered tools will allow for more sophisticated and rapid detection of anomalies and threats, enabling proactive security measures. Zero-trust security models will likely become more widespread, requiring continuous authentication and authorization for all users and systems, regardless of location or network access.
The importance of data minimization and user privacy will also become more crucial. A heightened emphasis on user data privacy and control will lead to more stringent data handling practices and user-friendly privacy controls. For instance, companies might introduce tools that allow users to access and control their data more easily, fostering greater transparency and accountability.
Impact on User Trust
The data breach will undoubtedly impact user trust in tech companies. Companies will need to demonstrate a strong commitment to security and transparency to rebuild trust with their users. This includes proactive communication about security incidents, clear explanations of response measures, and demonstrable steps taken to prevent future breaches. The importance of transparent communication and a user-centric approach will be crucial in mitigating the long-term impact on user trust.
Users are increasingly demanding more control over their data, and companies that prioritize transparency and user agency are more likely to retain their trust.
Ending Remarks
The Wyze data breach highlights the crucial need for robust security measures across the tech industry. From potential user account vulnerabilities to legal and regulatory implications, the incident has wide-reaching consequences. Ultimately, understanding this incident empowers users to take proactive steps to safeguard their accounts. This article provides a detailed analysis, offering a critical perspective on the breach and actionable steps for user protection.
Hopefully, lessons learned from this incident will lead to improved security practices in the future.