HTTP iframe injecting Linux rootkit is a sophisticated attack vector that exploits vulnerabilities in web servers to install malicious rootkits on Linux systems. This technique leverages the deceptive nature of iframes, embedding malicious code within seemingly harmless web pages, ultimately gaining unauthorized access and control. Understanding the mechanics, vulnerabilities, and mitigation strategies is crucial for securing systems against this threat.
The process typically involves a series of steps, from exploiting vulnerabilities in web servers to installing rootkits on targeted Linux machines. Attackers often use social engineering tactics to trick users into visiting compromised websites. This detailed exploration will cover the technical aspects, real-world examples, and mitigation strategies to protect against this evolving threat.
Introduction to HTTP IFrame Injection
HTTP iframe injection is a web security vulnerability that allows attackers to inject malicious iframes into a legitimate website. This technique exploits vulnerabilities in web applications to manipulate the displayed content, potentially deceiving users or redirecting them to malicious websites. Understanding the mechanics and types of these attacks is crucial for mitigating risks.The fundamental mechanism involves exploiting the dynamic nature of web pages.
Attackers identify a susceptible application or website that allows user-supplied data to be embedded into the webpage’s source code. This data might include HTML code, such as an iframe tag, which can then be manipulated to display a malicious website or execute harmful actions. The injected iframe is often invisible or subtly disguised, making it hard for the user to detect the malicious activity.
Types of HTTP IFrame Injections
Different types of HTTP iframe injections target specific vulnerabilities. These methods leverage various techniques for exploitation.
Attacker Leverage
Attackers leverage this technique for various malicious purposes, including phishing, data theft, and malware distribution. A common tactic is to inject an iframe containing a login page that looks identical to the legitimate website’s login form. This redirects users to a fake login page where their credentials are captured.
Vulnerable IFrame Example
The following example demonstrates a vulnerable iframe implementation. This code highlights the potential for malicious injection.“`html
This page displays content from a user-supplied source:
“`In this example, the `src` attribute of the iframe is directly populated by user input. If the user input is not sanitized, an attacker could inject a malicious iframe with a harmful URL.
Linux Rootkits and Their Functionality
Linux rootkits are malicious software designed to gain unauthorized access and control over a Linux system. They are insidious threats because they often operate covertly, hiding their presence from the user and security tools. Understanding their components, methods of concealment, and avenues for resource acquisition is crucial for effective defense against these sophisticated attacks.Rootkits employ a wide array of techniques to mask their presence and activity.
This makes detection challenging, requiring advanced security measures and vigilance. These covert operations can have severe consequences, potentially leading to data breaches, system compromise, and long-term damage to the affected infrastructure.
Speaking of sneaky security vulnerabilities, HTTP iframe injecting Linux rootkits are a serious concern. Fortunately, checking out the latest gadget reviews can be just as fascinating. For example, the OnePlus Watch 2 digital crown smartwatches button of the month, oneplus watch 2 digital crown smartwatches button of the month , highlights the impressive tech advancements in wearables.
Still, understanding these attack vectors is crucial for protecting your systems from similar threats. These rootkit attacks exploit vulnerabilities in the system’s core, making them a significant security risk.
Components of a Linux Rootkit
Rootkits are typically composed of several key components that work together to achieve their malicious objectives. These include:
- Kernel Modules: These modules are loaded into the Linux kernel, providing the rootkit with direct access to core system functions. This gives the rootkit deep control over the operating system. They manipulate system calls and other critical processes.
- User-Space Programs: These programs run in user mode and act as a front end for the rootkit’s functionality. They may include utilities for monitoring and controlling the system or for exfiltrating data. These are often less visible than kernel modules.
- Hidden Files and Directories: Rootkits can create and manipulate hidden files and directories to conceal their presence from typical file system inspections. These techniques make it harder to detect the malicious presence through standard file listing commands.
- Process Hides: Rootkits often hide or alter the display of processes in the system’s process list, obscuring their malicious activities.
Methods of Hiding Presence
Rootkits employ various methods to evade detection. These techniques often involve manipulating system logs, modifying system calls, and altering the system’s overall behavior to obscure their malicious activity.
- System Call Interception: Rootkits intercept and redirect system calls, allowing them to modify or manipulate the system’s response to specific requests. This can make the rootkit appear as a legitimate part of the operating system.
- Log Manipulation: Rootkits can modify or delete system logs, preventing security tools and administrators from detecting their presence or actions.
- Process Hiding: Rootkits often mask their processes to avoid detection by security tools that scan for suspicious or unusual processes.
- File System Alteration: Modifying the file system is a key part of concealing rootkit activity. This involves hiding files, directories, and even entire file systems.
Access to System Resources
Rootkits gain access to system resources through various methods. These methods exploit vulnerabilities in the system or user interactions, such as compromised accounts or exploits.
- Exploiting Vulnerabilities: Rootkits can exploit security holes in the system to gain initial access, potentially from remote attacks or vulnerabilities in the system’s software.
- Compromised Accounts: A common method is gaining access through a compromised user account or password. This often occurs through phishing or other social engineering attacks.
- Malicious Code Execution: The rootkit may be installed by executing malicious code, often via downloaded files or infected software.
Common Types of Linux Rootkits
Various types of rootkits target Linux systems, each with specific methods and capabilities. Some common types include:
- Kernel-level rootkits: These rootkits directly modify the kernel, providing extensive control over the system.
- User-level rootkits: These rootkits operate in user space, typically concealing their presence through various methods like log manipulation.
- File system rootkits: These rootkits manipulate the file system to hide files and directories, making it harder for security tools to identify malicious activities.
Rootkit Evasion Techniques Comparison
| Technique | Description | Detection Method | Impact |
|---|---|---|---|
| System Call Interception | Redirecting system calls to mask activities. | Analyzing system call traces, using specialized tools. | Difficult to detect malicious behavior. |
| Log Manipulation | Altering or deleting system logs to hide actions. | Monitoring log files for inconsistencies, using log analysis tools. | Conceals the timeline of attacks. |
| Process Hiding | Masking or modifying process listings. | Using process monitoring tools, checking for suspicious process names. | Makes identifying malicious processes challenging. |
| File System Alteration | Hiding or manipulating files and directories. | Using file system integrity checkers, scanning for hidden files. | Compromises data integrity and access control. |
Linking IFrame Injection to Linux Rootkit Installation
HTTP iframe injection, when combined with malicious intent, can serve as a vector for deploying Linux rootkits. Attackers leverage the trust associated with legitimate websites to trick unsuspecting users into executing malicious code, thereby gaining unauthorized access to their systems. This technique capitalizes on vulnerabilities in the target’s browser and operating system. A compromised system can then become a launchpad for further attacks, potentially leading to widespread damage.
Attack Process Overview
The process of using HTTP iframe injection to install a Linux rootkit involves several stages, starting with the attacker gaining control of a web server or a compromised website. This control enables the attacker to inject malicious code into the website’s HTML, which is then delivered to the victim’s system. The victim’s interaction with the compromised website triggers the execution of this malicious code, initiating the rootkit installation.
Injection Process Steps
The following steps Artikel the typical injection process:
1. Compromise the Web Server The attacker gains control over a web server, either through vulnerabilities or malicious activity. This grants them the ability to modify web pages and inject malicious code.
2. Malicious Code Insertion The attacker inserts a malicious iframe tag into the compromised website’s HTML. This iframe points to a remote server hosting the rootkit installation script. The code often masks its malicious intent within seemingly innocuous website content.
3. Triggering the Injection The victim accesses the compromised website, unknowingly interacting with the malicious iframe. The iframe’s execution triggers the download and execution of the rootkit installation script.
4. Rootkit Installation The rootkit installation script, delivered through the iframe, exploits vulnerabilities in the victim’s system to install the rootkit. This often involves executing a series of commands to achieve persistence and gain privileged access.
5. Persistence and Concealment The rootkit establishes persistence in the system, ensuring it remains active even after system reboots. It also often employs concealment techniques to avoid detection by security software.
Malicious Code Delivery
Malicious code can be delivered through various methods, each exploiting different aspects of the system. A crucial aspect of the attack is to disguise the malicious nature of the code within seemingly harmless content.
Payload Delivery Vectors
Different methods can be used to deliver the malicious payload embedded within the iframe, exploiting various vulnerabilities in the target’s environment.
| Vector | Description | Example | Vulnerability |
|---|---|---|---|
| Cross-Site Scripting (XSS) | Exploiting vulnerabilities in web applications to inject malicious scripts. | Inserting JavaScript code into a vulnerable forum post. | Vulnerable web application |
| Malicious Advertisements | Using advertisements to deliver malicious code. | Displaying an iframe within an advertisement banner. | Vulnerable advertisement platform |
| Social Engineering | Tricking the user into visiting a malicious website. | Phishing email containing a link to a malicious website. | User’s trust and awareness |
| Compromised Content Delivery Networks (CDNs) | Leveraging a compromised CDN to distribute the malicious code. | Malicious code embedded within a CDN-served website. | Compromised CDN |
Exploiting Vulnerabilities in the Process
HTTP iframe injection, coupled with Linux rootkits, relies heavily on vulnerabilities within web servers. Attackers meticulously target these weaknesses to gain unauthorized access and install malicious software. Understanding these vulnerabilities is crucial for implementing robust security measures to prevent such attacks.
Common Web Server Vulnerabilities
Web servers are complex systems, and various components can be vulnerable to exploitation. Common weaknesses include insecure configurations, outdated software, and vulnerabilities in the underlying operating system. These vulnerabilities often stem from a lack of proper maintenance, patching, and security best practices.
Exploitation Techniques
Attackers leverage several methods to exploit identified vulnerabilities. A common tactic involves crafting malicious payloads, such as specially crafted HTML code, to exploit vulnerabilities in the server’s interpretation of user requests. These payloads can then be disguised within seemingly harmless web content. Another method involves exploiting vulnerabilities in the server-side scripting language or the underlying operating system.
Sophisticated attackers may even use automated tools to probe for and exploit known vulnerabilities.
Attack Paths
Attack paths often involve a chain of vulnerabilities. For example, an attacker might first exploit a cross-site scripting (XSS) vulnerability to inject malicious JavaScript into a legitimate website. This JavaScript can then be used to communicate with a command-and-control server, allowing the attacker to download and install the rootkit. Similarly, a misconfigured file upload mechanism could allow attackers to upload malicious files, which, when executed, would grant them unauthorized access.
In many cases, a combination of vulnerabilities, such as outdated libraries or poorly secured authentication mechanisms, is used to create an effective attack path.
Mitigation Strategies
Mitigating these vulnerabilities requires a multi-layered approach. Regular security audits and vulnerability scans can identify potential weaknesses. Keeping software updated with the latest security patches is crucial. Strong access controls and authentication mechanisms should be implemented to limit the impact of successful attacks. Implementing input validation and output encoding techniques can prevent attackers from injecting malicious code.
Employing a Web Application Firewall (WAF) can help filter malicious traffic and block known attacks.
Security Misconfigurations
Properly configuring web servers is essential for preventing exploitation. Incorrect configurations can leave systems vulnerable to various attacks. The table below highlights common security misconfigurations that can be exploited for HTTP iframe injection attacks leading to Linux rootkit installation.
| Misconfiguration | Description | Impact | Mitigation |
|---|---|---|---|
| Open Directory Listing | Web server allows directory listings without proper access control. | Attackers can enumerate files and potentially discover sensitive information or vulnerable files. | Implement proper directory access control. Use .htaccess or equivalent mechanisms to restrict directory access. |
| Unrestricted File Uploads | Web server does not validate or sanitize uploaded files, allowing attackers to upload malicious scripts or executable files. | Attackers can execute arbitrary code on the server, potentially leading to remote code execution. | Implement strict file type validation, sanitization, and storage controls. Only allow uploads of specific file types. |
| Outdated Software | Web server software or supporting libraries are not updated with the latest security patches. | Attackers can exploit known vulnerabilities in outdated components. | Regularly update all software components to the latest patched versions. Establish a robust patching schedule. |
| Missing or Weak Input Validation | Web server does not validate user input, allowing attackers to inject malicious code. | Attackers can inject malicious scripts or commands, leading to cross-site scripting (XSS) attacks or other vulnerabilities. | Validate and sanitize all user inputs before processing them. Implement output encoding techniques to prevent reflected XSS attacks. |
Security Implications and Mitigation Strategies
The successful exploitation of an HTTP iframe injection vulnerability leading to Linux rootkit installation poses severe security risks to the targeted system and the wider network. This attack vector can compromise critical infrastructure, steal sensitive data, and potentially disrupt operations. Understanding the potential impact and implementing robust mitigation strategies is crucial to prevent such incidents.Compromised systems become launchpads for further malicious activities.
Attackers can use the compromised machine to spread malware to other systems on the network, launch denial-of-service attacks, or exfiltrate valuable data. The impact can ripple throughout an organization, affecting its reputation, financial standing, and operational efficiency.
Potential Impact of Successful Attacks, Http iframe injecting linux rootkit
A successful attack can have devastating consequences. The compromised system may be used as a springboard for further attacks on other systems within the network, potentially compromising the entire infrastructure. Attackers can deploy various malicious payloads, including ransomware, data theft tools, and other harmful software. The impact can range from data breaches and financial losses to operational disruption and reputational damage.
In severe cases, critical infrastructure could be severely impacted, potentially leading to significant disruptions. For example, a rootkit installed on a financial institution’s server could lead to fraudulent transactions and significant financial losses.
Potential Consequences of a Compromised System
The consequences of a compromised system can be far-reaching. Stolen data can be used for identity theft, fraud, or other malicious purposes. The compromised system can become a platform for further attacks on other systems, extending the scope of the damage. Compromised systems can be used to launch denial-of-service attacks, disrupting legitimate services and causing significant financial losses.
The compromised system may be used to spy on users, collect sensitive information, or install additional malicious software. Moreover, the attacker can maintain stealthy access to the system for extended periods, leading to a more sophisticated attack.
Security Measures to Prevent Attacks
Implementing robust security measures is paramount in preventing HTTP iframe injection attacks that lead to Linux rootkit installations. These measures should encompass both network-level and system-level defenses. Regular security audits, proactive vulnerability assessments, and incident response planning are essential components of a comprehensive security strategy. Patching known vulnerabilities promptly is crucial.
Robust Defenses Against This Type of Attack
A multi-layered approach to security is necessary to counter the multifaceted nature of this attack. This includes strengthening web application firewalls (WAFs) to detect and block malicious iframe injections. Regularly updating software and operating systems to address known vulnerabilities is critical. Employing intrusion detection and prevention systems (IDS/IPS) can detect malicious traffic patterns and block attacks. Furthermore, implementing strong access controls and user authentication mechanisms can limit the potential impact of a successful compromise.
Network segmentation can isolate compromised systems, preventing the spread of malware.
Summary of Preventative Measures
| Measure | Description | Implementation | Effectiveness |
|---|---|---|---|
| Regular Vulnerability Assessments | Identifying and addressing potential security weaknesses in systems and applications. | Employ automated tools and manual assessments to scan for known vulnerabilities. | High, if conducted frequently and with a focus on the specific attack vectors. |
| Strong Authentication | Implementing robust user authentication methods to prevent unauthorized access. | Using multi-factor authentication, strong passwords, and access control lists. | High, when combined with other security measures. |
| Network Segmentation | Dividing the network into smaller, isolated segments to contain the spread of malware. | Using firewalls and VLANs to create logical boundaries. | Medium to High, depending on the thoroughness of implementation and network design. |
| Proactive Patch Management | Promptly applying security patches to operating systems and applications. | Establish a clear patch management process and adhere to a schedule. | High, if patches are deployed quickly and consistently. |
| Intrusion Detection/Prevention Systems (IDS/IPS) | Monitoring network traffic for malicious activity and blocking suspicious connections. | Deploy IDS/IPS devices and configure them appropriately. | Medium to High, depending on the effectiveness of the IDS/IPS signature database. |
Real-World Examples and Case Studies: Http Iframe Injecting Linux Rootkit
Real-world examples of HTTP iframe injection attacks, often used in conjunction with Linux rootkit installations, demonstrate the devastating impact these techniques can have on organizations. Understanding these past incidents provides valuable insights into the tactics employed, the vulnerabilities exploited, and the crucial security measures that can be implemented to prevent future attacks. This examination sheds light on the evolving nature of cyber threats and highlights the need for continuous vigilance and adaptation in the face of ever-changing attack methodologies.
Speaking of sneaky tech, http iframe injecting Linux rootkits are a serious security threat. They’re like digital ninjas, hiding in plain sight. Fortunately, understanding these tactics is key to defense, and keeping tabs on the latest developments in the security world is vital. Luckily, the Fortnite Rift Tour concert series offers a great distraction, but remember, security is paramount.
It’s important to remember that these kinds of attacks can affect various systems and applications, requiring a multi-faceted approach to prevention.
Illustrative Examples of Attacks
Several instances of HTTP iframe injection attacks have been documented, where attackers leveraged vulnerabilities to gain unauthorized access to systems and deploy rootkits. These attacks often involve sophisticated techniques that exploit vulnerabilities in web applications and operating systems. The effectiveness of these attacks hinges on exploiting weaknesses in the target’s security posture.
- Example 1: The “Shadow Broker” Leak: The release of hacking tools, including those for exploiting vulnerabilities in web servers and operating systems, demonstrated the capability to inject malicious iframes into legitimate websites. This allowed attackers to install rootkits on vulnerable systems. The leak highlighted the potential for widespread attacks leveraging readily available tools, emphasizing the importance of regular security audits and patching.
Attackers can exploit vulnerabilities in web applications and operating systems to install rootkits. The consequences included data breaches, system compromise, and significant reputational damage to organizations.
- Example 2: Targeted Attacks on Financial Institutions: Sophisticated attackers have targeted financial institutions, leveraging vulnerabilities in web applications to inject malicious iframes. These iframes, often disguised as legitimate content, can lead to the installation of rootkits, allowing attackers to gain access to sensitive financial data. The consequences of these attacks could be substantial, involving financial losses, reputational damage, and legal repercussions. This example underlines the critical need for robust security measures to prevent attacks against financial institutions.
- Example 3: Supply Chain Attacks: Attackers have infiltrated software supply chains to install malicious code. This includes injecting malicious iframes into legitimate websites or tools used by developers or other personnel. The attackers then use the compromised tools or websites to inject rootkits into targeted systems, often bypassing traditional security measures. This method underscores the importance of secure development practices and robust supply chain security controls.
The consequences include significant damage to organizations, potentially including the compromise of sensitive data and disruption of operations.
Vulnerabilities Exploited
A variety of vulnerabilities are exploited in these attacks, which often exploit vulnerabilities in web servers, web applications, or client-side software. These vulnerabilities can be exploited by attackers to gain access to systems and deploy rootkits. A key vulnerability is the lack of proper validation or sanitization of user-supplied data, allowing attackers to inject malicious code. Additionally, outdated or unpatched software is a frequent target for these attacks.
It’s essential to understand the specific vulnerabilities that can be exploited to effectively implement appropriate mitigation strategies.
HTTP iframe injecting Linux rootkits is a sneaky attack vector. It’s all about exploiting vulnerabilities to gain unauthorized access, often disguised as legitimate content. This type of attack can be devastating, especially in the context of a defaced Starman NFT artist page, like the one recently seen with Jim Henson, Shigeru Miyamoto, and crypto art from Starmaker. This recent incident highlights the importance of robust security measures for protecting sensitive data, and underscores the need for vigilance against these types of attacks on digital assets.
Ultimately, the threat of HTTP iframe injecting Linux rootkits remains a real concern in the online world.
| Example | Description | Attack Vector | Vulnerability |
|---|---|---|---|
| The “Shadow Broker” Leak | Release of hacking tools | Exploiting vulnerabilities in web servers and operating systems | Outdated or unpatched software, lack of proper validation of user-supplied data |
| Targeted Attacks on Financial Institutions | Sophisticated attacks on financial institutions | Vulnerabilities in web applications | Cross-Site Scripting (XSS), insecure Direct Object References (IDOR) |
| Supply Chain Attacks | Infiltration of software supply chains | Injecting malicious code into legitimate websites or tools | Vulnerabilities in development tools or software supply chains, insufficient security checks |
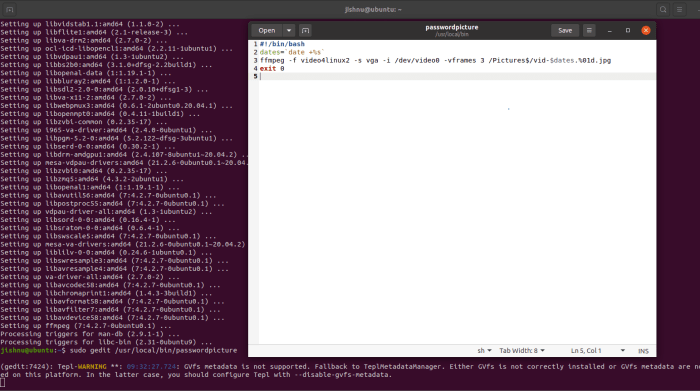
Technical Deep Dive: Analysis of the Process
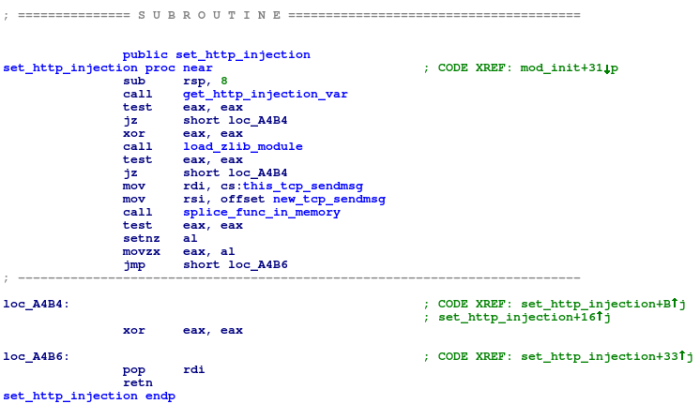
This section delves into the intricate details of an HTTP iframe injection attack targeting Linux systems, focusing on the code execution flow, rootkit component loading and activation, persistence mechanisms, and evasion techniques. Understanding these components is crucial for developing effective security defenses.
Code Execution Flow
The attack typically begins with a compromised web server serving a malicious webpage. This webpage contains an iframe element that dynamically loads a specially crafted payload. This payload, often disguised as a seemingly benign resource, contains the rootkit’s core components. When a user’s browser loads the malicious page, the iframe initiates the download of the rootkit components.
The subsequent steps depend on the specific rootkit’s design.
Rootkit Component Loading and Activation
Once the rootkit components are downloaded, a critical step involves loading and activating them. This process usually involves carefully crafted code within the payload, utilizing system calls to access and modify kernel structures. The rootkit’s components may be loaded into memory, potentially utilizing memory mapping techniques to hide their presence. Activation involves registering callbacks, hooks, and drivers within the operating system.
This often happens after the initial payload execution.
Persistence Mechanisms
Maintaining persistent access is a key objective for rootkits. Several techniques are used, including:
- Modifying system startup processes: Rootkits can modify system initialization scripts to ensure that their components are loaded every time the system boots. This involves modifying configuration files or inserting code into critical initialization routines.
- Creating scheduled tasks: Employing the system’s task scheduling capabilities, the rootkit can arrange for its own execution at regular intervals, enabling persistent presence. This allows for continuous monitoring and control.
- Utilizing services or daemons: The rootkit may create or modify existing services or daemons to run as background processes. This ensures that the rootkit continues operating even after the user session ends.
Evasion Techniques
Rootkits employ various methods to evade detection. These techniques aim to mask their presence from antivirus software, intrusion detection systems, and other security tools. These methods include:
- Code obfuscation: Complicating the rootkit’s code makes it harder for analysis tools to identify malicious patterns. Techniques include encrypting or compressing the code and using complex control flow graphs.
- Using system call bypasses: Rootkits may exploit system call mechanisms to avoid detection by antivirus software. This involves bypassing normal security checks.
- Dynamic patching: Rootkits can modify system libraries and kernel modules at runtime, making it difficult for static analysis tools to detect malicious activities.
Code Snippet Example
// Example (Illustrative - Not executable code) #include <sys/types.h> #include <sys/stat.h> #include <unistd.h> #include <stdlib.h> int main() // ... (code to download rootkit components) ... // ... (code to load rootkit components into memory) ... // ... (code to register callbacks for key system calls) ... // ... (code to modify system startup scripts) ... return 0;
This snippet, while not actual malicious code, demonstrates the general structure of the attack, highlighting the critical steps involved in downloading, loading, and activating the rootkit.
Detection and Response Mechanisms
HTTP iframe injection attacks, while often subtle, leave traces that vigilant systems can detect. Proactive monitoring and robust incident response procedures are crucial for mitigating the damage and preventing further compromise. Early detection allows for swift containment and minimizes the potential for broader exploitation.
Effective detection hinges on understanding the attack patterns and the telltale signs of malicious activity. This involves analyzing web traffic, examining system logs, and monitoring for unusual user behavior. A multi-layered approach is essential for comprehensive protection.
Identifying HTTP Iframe Injection Attempts
Malicious iframe injections often manifest as unexpected changes in website behavior or presentation. Users might notice unexpected redirects, altered content, or the appearance of unfamiliar elements. Monitoring user activity logs, particularly for unusual browsing patterns or access to restricted resources, can highlight suspicious activity. Analysis of web server logs for unusual traffic patterns, like increased requests to malicious domains or sudden spikes in specific resource requests, is also vital.
Tools and Methods for Identifying Malicious Activity
Various tools and techniques can assist in detecting and analyzing potential threats. Network traffic analysis tools can capture and decode network packets, revealing anomalies and malicious code injections. Security information and event management (SIEM) systems aggregate security logs from various sources, providing a centralized view of potential threats. Web application firewalls (WAFs) can detect and block malicious traffic based on predefined rules and signatures.
Intrusion detection systems (IDS) actively monitor network traffic for suspicious activity and can trigger alerts when specific patterns, such as iframe injections, are identified.
Incident Response Procedures
A well-defined incident response plan is critical for handling attacks effectively. The plan should Artikel steps to take upon detecting an attack, including isolating affected systems, containing the spread, and restoring systems to a known good state. This involves identifying the source of the attack, determining the extent of the damage, and implementing appropriate countermeasures. Communication protocols should be in place to keep stakeholders informed throughout the process.
Furthermore, a detailed post-incident analysis is crucial to understanding the attack vector and improving future security posture.
Steps to Take After Detecting an Attack
Immediately upon detection, isolate the compromised system or affected user accounts to prevent further propagation. Document all steps taken during the response process. Investigate the attack vector to understand how the attacker gained access and identify vulnerabilities that need remediation. Remediate any identified vulnerabilities to prevent future attacks. Restore affected systems to a known good state.
Detection Tools and Their Functionalities
| Tool | Functionality | Pros | Cons |
|---|---|---|---|
| Wireshark | Network protocol analyzer for capturing and examining network traffic. Can identify unusual traffic patterns and decipher malicious code injections. | Open-source, highly customizable, excellent for detailed analysis. | Requires technical expertise to interpret results, can generate large amounts of data. |
| Snort | Network intrusion detection system (IDS) that monitors network traffic for malicious activity based on predefined rules and signatures. | Open-source, versatile rule-set, can be customized for specific threats. | Requires careful rule configuration to avoid false positives, needs ongoing updates to stay current with evolving threats. |
| Elasticsearch, Logstash, Kibana (ELK Stack) | Centralized log management and analysis platform. Collects logs from various sources, allowing for correlation and pattern recognition. | Powerful search capabilities, visual dashboards, great for threat hunting and correlation. | Can be complex to set up and maintain, requires significant computational resources. |
| OWASP ModSecurity | Open-source web application firewall (WAF) that can detect and block malicious HTTP requests. Can be configured to detect and block iframe injection attempts. | Flexible rules and configurations, open-source. | Requires significant configuration and ongoing maintenance to stay updated. |
Final Review
In conclusion, http iframe injecting Linux rootkits represents a potent attack strategy. Understanding the intricacies of this technique, from the initial injection to the installation of rootkits, is essential for proactive defense. Implementing robust security measures, such as vulnerability scanning, regular updates, and user awareness training, is paramount to mitigate this evolving threat landscape. By combining technical knowledge with proactive security measures, organizations can effectively safeguard their Linux systems from this sophisticated attack.